 本文由
创作,已纳入「FreeBuf原创奖励计划」,未授权禁止转载
本文由
创作,已纳入「FreeBuf原创奖励计划」,未授权禁止转载
前记
许多EDR产品常见的操作是将他们的DLL注入到其想监测的进程中,寻找前辈们的防注入思路发现大概有以下两种,分别是:
1、PROCESS_CREATION_MITIGATION_POLICY_BLOCK_NON_MICROSOFT_BINARIES_ALWAYS_ON会阻止不带微软签名的DLL加载
2、ProcessDynamicCodePolicy禁用了VirtualProtect和分配RWX内存可能会强制阻止一个带微软签名的DLL加载
于是分别测试实战效果(这里仅以普通dll注入,即远程LoadLibrary加载而非创建远程线程)
blockdlls
#include <Windows.h>
int main()
{
STARTUPINFOEXA si = {0};
PROCESS_INFORMATION pi = { 0 };
SIZE_T size = 0;
BOOL ret;
// Required for a STARTUPINFOEXA
si.StartupInfo.cb = sizeof(STARTUPINFOEXA);
// Get the size of our PROC_THREAD_ATTRIBUTE_LIST to be allocated
InitializeProcThreadAttributeList(NULL, 1, 0, &size);
// Allocate memory for PROC_THREAD_ATTRIBUTE_LIST
si.lpAttributeList = (LPPROC_THREAD_ATTRIBUTE_LIST)HeapAlloc(
GetProcessHeap(),
HEAP_ZERO_MEMORY,
size
);
// Initialise our list
InitializeProcThreadAttributeList(si.lpAttributeList, 1, 0, &size);
// Enable blocking of non-Microsoft signed DLLs
DWORD64 policy = PROCESS_CREATION_MITIGATION_POLICY_BLOCK_NON_MICROSOFT_BINARIES_ALWAYS_ON;
// Assign our attribute
UpdateProcThreadAttribute(si.lpAttributeList, 0, PROC_THREAD_ATTRIBUTE_MITIGATION_POLICY, &policy, sizeof(policy), NULL, NULL);
// Finally, create the process
ret = CreateProcessA(
NULL,
(LPSTR)"C:\\Windows\\System32\\notepad.exe",
NULL,
NULL,
true,
EXTENDED_STARTUPINFO_PRESENT,
NULL,
NULL,
reinterpret_cast<LPSTARTUPINFOA>(&si),
&pi
);
}
这里通过UpdateProcThreadAttribute 添加lpAttributeList中PROC_THREAD_ATTRIBUTE_MITIGATION_POLICY属性为PROCESS_CREATION_MITIGATION_POLICY_BLOCK_NON_MICROSOFT_BINARIES_ALWAYS_ON,然后创建的进程如图:Only Microsoft signatures are allowed.
有用但是用处不大,因为发现大多数EDR使用有效的Microsoft签名来对抗该策略!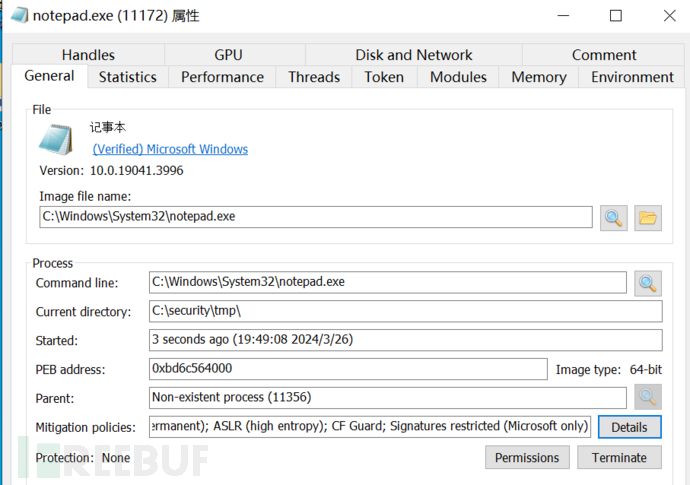
ACG
ProcessDynamicCodePolicyis also sometimes called Arbitrary Code Guard (ACG)
ACG是Windows系统的另一个安全策略,具体如下
1、现有代码被修改(代码页不能变为可写);
2、在数据段上写入代码并执行(数据不能变为代码)。
即不能申请和修改同时具有写入(W)和执行(X)的权限
#include <iostream>
#include <Windows.h>
#include <processthreadsapi.h>
int main()
{
STARTUPINFOEX si;
DWORD oldProtection;
PROCESS_MITIGATION_DYNAMIC_CODE_POLICY policy;
ZeroMemory(&policy, sizeof(policy));
policy.ProhibitDynamicCode = 1;
void* mem = VirtualAlloc(0, 1024, MEM_RESERVE | MEM_COMMIT, PAGE_EXECUTE_READWRITE);
if (mem == NULL) {
printf("[!] Error allocating RWX memory\n");
}
else {
printf("[*] RWX memory allocated: %p\n", mem);
}
printf("[*] Now running SetProcessMitigationPolicy to apply PROCESS_MITIGATION_DYNAMIC_CODE_POLICY\n");
// Set our mitigation policy
if (SetProcessMitigationPolicy(ProcessDynamicCodePolicy, &policy, sizeof(policy)) == false) {
printf("[!] SetProcessMitigationPolicy failed\n");
return 0;
}
// Attempt to allocate RWX protected memory (this will fail)
mem = VirtualAlloc(0, 1024, MEM_RESERVE | MEM_COMMIT, PAGE_EXECUTE_READWRITE);
if (mem == NULL) {
printf("[!] Error allocating RWX memory\n");
}
else {
printf("[*] RWX memory allocated: %p\n", mem);
}
void* ntAllocateVirtualMemory = GetProcAddress(LoadLibraryA("ntdll.dll"), "NtAllocateVirtualMemory");
// Let's also try a VirtualProtect to see if we can update an existing page to RWX
if (!VirtualProtect(ntAllocateVirtualMemory, 4096, PAGE_EXECUTE_READWRITE, &oldProtection)) {
printf("[!] Error updating NtAllocateVirtualMemory [%p] memory to RWX\n", ntAllocateVirtualMemory);
}
else {
printf("[*] NtAllocateVirtualMemory [%p] memory updated to RWX\n", ntAllocateVirtualMemory);
}
system("pause");
}
[*] RWX memory allocated: 0000018B24D70000
[*] Now running SetProcessMitigationPolicy to apply PROCESS_MITIGATION_DYNAMIC_CODE_POLICY
[!] Error allocating RWX memory
[!] Error updating NtAllocateVirtualMemory [00007FFA9248F660] memory to RWX
尝试本地注入失败,但是远程dll注入和远程创建新线程均可以成功,正如下面所言
But actually, ACG doesn’t block a remote processes ability to call a function such as
VirtualAllocEx.Unfortunately there doesn’t appear to be a way to set the Process Mitigation policy when calling CreateProcess either
看到有研究者写到:
许多EDR产品常见的操作是将他们的DLL注入到其想监测的进程中,围绕特定的API函数实现用户态hook技术(参考文章)。由于hook技术通常需要修改现有的可执行内存页以添加hook,因此EDR通常需要调用VirtualProtect来更新内存保护。如果我们在恶意软件设计上启用ProcessDynamicCodePolicy可能有助于保护其免受EDR hook监测的影响
然而并不现实,EDR通常在我们的进程刚启动的时候就已经完成注入和内存修改并进行hook,而我们后续的属性设定操作是在edr的dll注入之后才完成的,并且我们没法在创建之前就设定该属性
结论
签名策略和ACG不太可能帮助防止反病毒供应商的DLL注入,而考虑采取以下措施:
Reload the hooked DLL’s from disk
Modify the injected DLL’s to make sure they don’t take action
Attempt direct system calls to bypass the hooks
测试代码
a.dll
#include<windows.h>
#include "pch.h"
int a=10;
BOOL APIENTRY DllMain(HMODULE hModule,
DWORD ul_reason_for_call,
LPVOID lpReserved
)
{
switch (ul_reason_for_call)
{
case DLL_PROCESS_ATTACH:
case DLL_THREAD_ATTACH:
case DLL_THREAD_DETACH:
case DLL_PROCESS_DETACH:
break;
}
return TRUE;
}
inject.exe
#include <windows.h>
#include <stdio.h>
#include <TlHelp32.h>
typedef FARPROC
(WINAPI
* pGetProcAddress)(
_In_ HMODULE hModule,
_In_ LPCSTR lpProcName
);
typedef HMODULE
(WINAPI
* pLoadLibraryA)(
_In_ LPCSTR lpLibFileName
);
BOOL mydllinject(DWORD pid, LPCTSTR szDllPath);
int main(int argc, char* argv[])
{
DWORD pid = (DWORD)atoi(argv[1]);
printf("%d", pid);
mydllinject(pid, L"a.dll");
system("pause");
return 0;
}
BOOL mydllinject(DWORD pid, LPCTSTR szDllPath)
{
HMODULE hMod = GetModuleHandle(L"kernel32.dll");
pGetProcAddress pThreadProc = (pGetProcAddress)GetProcAddress(hMod, "LoadLibraryW");
HANDLE hProcess = OpenProcess(PROCESS_ALL_ACCESS, FALSE, pid);
if (hProcess == NULL)
{
return FALSE;
}
DWORD size = (DWORD)(wcslen(szDllPath) + 1) * sizeof(TCHAR);
LPVOID conAddr = VirtualAllocEx(hProcess, NULL, size, MEM_COMMIT, PAGE_READWRITE);
if (conAddr == NULL)
{
return FALSE;
}
printf("add:%x", conAddr);
int writecon = WriteProcessMemory(hProcess, conAddr, (LPCVOID)szDllPath, size, NULL);
if (writecon == 0)
{
printf("WriteProcessMemory:%d\n", GetLastError());
}
HANDLE thred = CreateRemoteThread(hProcess, NULL, 0, (LPTHREAD_START_ROUTINE)pThreadProc, conAddr, 0, NULL);
if (thred == NULL)
{
printf("CreateRemoteThread:%d\n", GetLastError());
}
WaitForSingleObject(thred, INFINITE);
}
reference
https://www.cnblogs.com/zha0gongz1/p/15391205.html
https://blog.xpnsec.com/protecting-your-malware/





