关于ProtectMyTooling
ProtectMyTooling是一个包含了大量封装器的工具框架,该工具可以帮助广大研究人员以菊花链的形式将各种封装器、混淆工具、编码解码器和其他红队研究工具串联起来,并包含了工具水印、IoC收集和PE后门等功能,因此该工具也是一个功能强大的网络安全框架。
在ProtectMyTooling的帮助下,我们可以快速混淆二进制文件,而无需点击各种界面、菜单和对话框。ProtectMyTooling提供了非常简单易用的接口,而且可以在一个代码文件上以菊花链的形式串联多个处理工具来对其进行处理。
功能介绍
1、支持多个不同的PE封装器、.NET混淆工具、Shellcode加载器/构建器;
2、支持以菊花链的形式串联封装器;
3、支持收集IoC;
4、提供了自定义水印注入;
5、提供了方便的CobaltStrike Aggressor脚本,提供了protected-upload和protected-execute-assembly命令;
6、简单易用的命令行;
工具安装
该工具专为Windows系统设计,但某些功能仍然可以在Linux上正常运行。
首先,请禁用你的反病毒产品,然后将contrib目录添加到排除路径中。这个目录中包含了模糊处理器和AV可能会标记和删除的一些其他组件。
然后使用下列命令将该项目源码克隆至本地:
PS C:\> git clone --recurse https://github.com/Binary-Offensive/ProtectMyTooling
Windows安装
PS C:\ProtectMyTooling> .\install.ps1
Linux安装
bash# ./install.sh
如果使用的是Windows 10,则需要安装Golang(v1.16+)环境:
cmd> bash bash$ sudo apt update ; sudo apt upgrade -y ; sudo apt install golang=2:1.18~3 -y
工具使用
在首次使用ProtectMyTooling之前,请先调整的程序的YAML规则文件ProtectMyTooling.yaml。参数处理顺序如下:
1、首先,工具会读取和使用默认参数;
2、然后它们的值会被YAML规则文件中的值覆盖;
3、命令行中提供的值会覆盖所有的值;
使用场景1:ConfuserEx混淆
C:\> py ProtectMyTooling.py confuserex Rubeus.exe Rubeus-obf.exe ::::::::::.:::::::.. ... :::::::::::.,:::::: .,-:::::::::::::::: `;;;```.;;;;;;``;;;; .;;;;;;;;;;;;;;;\''';;;;\'\''',;;;'````;;;;;;;;\'\''' `]]nnn]]' [[[,/[[[' ,[[ \[[, [[ [[cccc [[[ [[ $$$"" $$$$$$c $$$, $$$ $$ $$"""" $$$ $$ 888o 888b "88bo"888,_ _,88P 88, 888oo,_`88bo,__,o, 88, . YMMMb :.-:.MM ::-. "YMMMMMP" MMM """"YUMMM"YUMMMMMP" MMM ;;,. ;;;';;. ;;;;' [[[[, ,[[[[, '[[,[[[' $$$$$$$$"$$$ c$$" 888 Y88" 888o,8P"` ::::::::::::mM... ... ::: :::::. :::. .,-:::::/ ;;;;;;;;\'''.;;;;;;;. .;;;;;;;. ;;; ;;`;;;;, `;;,;;-'````' [[ ,[[ \[[,[[ \[[,[[[ [[[ [[[[[. '[[[[ [[[[[[/ $$ $$$, $$$$$, $$$$$' $$$ $$$ "Y$c$"$$c. "$$ 88, "888,_ _,88"888,_ _,88o88oo,._888 888 Y88`Y8bo,,,o88o MMM "YMMMMMP" "YMMMMMP"""""YUMMMMM MMM YM `'YMUP"YMM Red Team implants protection swiss knife. Multi-Packer wrapping around multitude of packers, protectors, shellcode loaders, encoders. Mariusz Banach / mgeeky '20-'22, <mb@binary-offensive.com> v0.16 [.] Processing x86 file: "\Rubeus.exe" [.] Generating output of ConfuserEx(<file>)... [+] SUCCEEDED. Original file size: 417280 bytes, new file size ConfuserEx(<file>): 756224, ratio: 181.23%
使用场景2:ConfuserEx混淆并进行测试
C:\> py ProtectMyTooling.py confuserex Rubeus.exe Rubeus-obf.exe -r --cmdline "hash /password:foobar" [...] [.] Processing x86 file: "\Rubeus.exe" [.] Generating output of ConfuserEx(<file>)... [+] SUCCEEDED. Original file size: 417280 bytes, new file size ConfuserEx(<file>): 758272, ratio: 181.72% Running application to test it... ______ _ (_____ \ | | _____) )_ _| |__ _____ _ _ ___ | __ /| | | | _ \| ___ | | | |/___) | | \ \| |_| | |_) ) ____| |_| |___ | |_| |_|____/|____/|_____)____/(___/ v2.0.0 [*] Action: Calculate Password Hash(es) [*] Input password : foobar [*] rc4_hmac : BAAC3929FABC9E6DCD32421BA94A84D4 [!] /user:X and /domain:Y need to be supplied to calculate AES and DES hash types!
使用场景3:复杂的恶意软件混淆(带水印和IoC收集)
PS> py .\ProtectMyTooling.py callobf,upx,hyperion beacon.exe beacon-obf.exe -i -I operation_chimera -w dos-stub=fooobar -w checksum=0xaabbccdd [...] [.] Processing x64 file: "beacon.exe" [>] Generating output of CallObf(<file>)... [.] Before obfuscation file's PE IMPHASH: 17b461a082950fc6332228572138b80c [.] After obfuscation file's PE IMPHASH: 378d9692fe91eb54206e98c224a25f43 [>] Generating output of UPX(CallObf(<file>))... [>] Generating output of Hyperion(UPX(CallObf(<file>)))... [+] Setting PE checksum to 2864434397 (0xaabbccdd) [+] Successfully watermarked resulting artifact file. [+] IOCs written to: beacon-obf-ioc.csv [+] SUCCEEDED. Original file size: 288256 bytes, new file size Hyperion(UPX(CallObf(<file>))): 175616, ratio: 60.92%
生成的IoC CSV文件如下:
timestamp,filename,author,context,comment,md5,sha1,sha256,imphash 2022-06-10 03:15:52,beacon.exe,mgeeky@commandoVM,Input File,test,dcd6e13754ee753928744e27e98abd16,298de19d4a987d87ac83f5d2d78338121ddb3cb7,0a64768c46831d98c5667d26dc731408a5871accefd38806b2709c66cd9d21e4,17b461a082950fc6332228572138b80c 2022-06-10 03:15:52,y49981l3.bin,mgeeky@commandoVM,Obfuscation artifact: CallObf(<file>),test,50bbce4c3cc928e274ba15bff0795a8c,15bde0d7fbba1841f7433510fa9aa829f8441aeb,e216cd8205f13a5e3c5320ba7fb88a3dbb6f53ee8490aa8b4e1baf2c6684d27b,378d9692fe91eb54206e98c224a25f43 2022-06-10 03:15:53,nyu2rbyx.bin,mgeeky@commandoVM,Obfuscation artifact: UPX(CallObf(<file>)),test,4d3584f10084cded5c6da7a63d42f758,e4966576bdb67e389ab1562e24079ba9bd565d32,97ba4b17c9bd9c12c06c7ac2dc17428d509b64fc8ca9e88ee2de02c36532be10,9aebf3da4677af9275c461261e5abde3 2022-06-10 03:15:53,beacon-obf.exe,mgeeky@commandoVM,Obfuscation artifact: Hyperion(UPX(CallObf(<file>))),test,8b706ff39dd4c8f2b031c8fa6e3c25f5,c64aad468b1ecadada3557cb3f6371e899d59790,087c6353279eb5cf04715ef096a18f83ef8184aa52bc1d5884e33980028bc365,a46ea633057f9600559d5c6b328bf83d 2022-06-10 03:15:53,beacon-obf.exe,mgeeky@commandoVM,Output obfuscated artifact,test,043318125c60d36e0b745fd38582c0b8,a7717d1c47cbcdf872101bd488e53b8482202f7f,b3cf4311d249d4a981eb17a33c9b89eff656fff239e0d7bb044074018ec00e20,a46ea633057f9600559d5c6b328bf83d
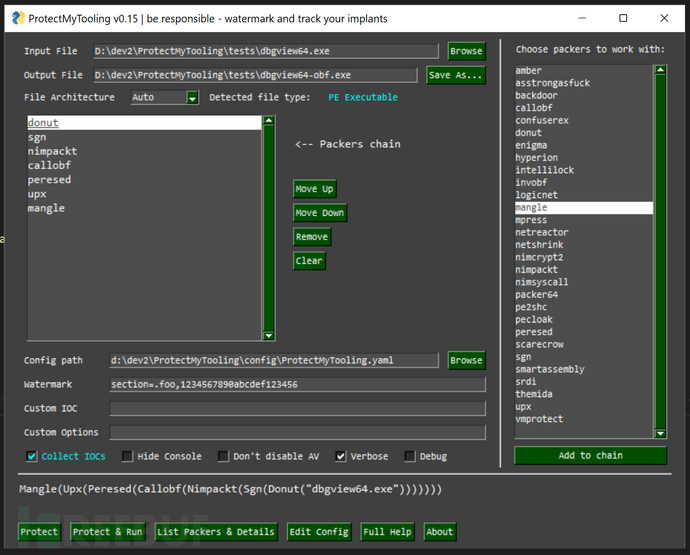
工具运行截图
项目地址
ProtectMyTooling:【GitHub传送门】
参考资料
如需授权、对文章有疑问或需删除稿件,请联系 FreeBuf 客服小蜜蜂(微信:freebee1024)





